Stop Data Loss Before It Leaves The Device




The problem
Hybrid work didn’t stretch your perimeter: it shattered it. Data now flows between home networks, SaaS apps, unmanaged Wi-Fi, and generative AI tools. Every upload, every share, every copied prompt is a potential leak. If you can’t see data in use, you can’t stop it from walking out the door.
Shadow AI is accelerating exposure
Employees are adopting AI tools faster than security policies can keep up. Sensitive data is being pasted into prompts, uploaded to unknown platforms, and shared across SaaS without oversight. The breach may not start with malware; it starts with a well-meaning employee and an ungoverned upload.
AI has changed the balance of power in cybersecurity. To keep up, organizations need intelligence that adapts as fast as the threats.
Shadow-proof your data: block the AI backdoor
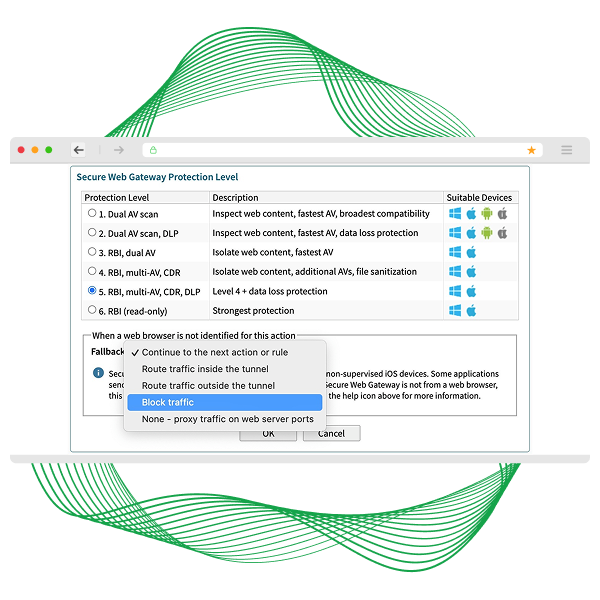
Stop chasing leaks after they happen. Enforce control at the endpoint. Secure Access applies inline DLP scanning and encryption directly on devices; governing uploads, shares, and GenAI prompts in real time. Sensitive data is inspected before it leaves the device, not after it reaches the cloud.
Granular policies block unauthorized AI tools, restrict risky SaaS uploads, and enforce encryption everywhere they work, without slowing users down.
Custom policy design for hybrid workforce security
AI can give your organization a true competitive advantage, but unchecked use is a ticking timebomb. See how you can control AI usage with Secure Access:
- Easily tailor policies to reduce risk of data exposure and stop access to risky sites without impacting user productivity.
- Get actionable insights from drilldown dashboards, and key metrics to reassure your SLT.



How Civeo secures data for hybrid and remote work
Discover how Civeo built a resilient, secure IT foundation to protect sensitive data across remote sites and hybrid environments.
- Rapid, Secure Deployments: Learn how Civeo eliminated complexity and enforced strong data protection in challenging locations.
- Full Visibility & Control: See how Absolute Secure Access enabled real-time diagnostics, incident response, and compliance at scale.
Data protection for hybrid workers: key capabilities
Govern uploads, shares, and GenAI prompts as they happen — not after the fact.
Apply controls that persist wherever work happens — remote, hybrid, or home network.
Detect and block AI tools and unsanctioned apps that expose sensitive data.
Ensure data remains encrypted in motion and at rest across networks and devices.
Adjust policy based on sensitivity, user context, and data type, with AI-Powered UEBA Analytics.
See exactly where sensitive data is and how it’s being used — with exportable compliance insight.
Lock down data—anywhere work happens with a modern SSE solution
Learn how Secure Access SaaS gives you unmatched security, efficiency, and scale - creating a resilient foundation that keeps your modern enterprise safe from evolving AI threats.
- Always-On Security: Enforce encryption, monitor compliance, and stop leaks—without slowing productivity.
- Hybrid-Ready Control: Gain visibility and control across every endpoint, no matter where work gets done.

Your data is moving. Are you in control?
Every upload, share, and AI prompt is a decision point. In a tailored Secure Access demo, see how endpoint-enforced DLP shuts down shadow risk, governs GenAI usage, and protects sensitive data everywhere work happens.
- Block Risky AI Prompts: Stop sensitive data from being pasted into GenAI tools before it leaves the device.
- Enforce Upload Governance in Real Time: Allow productivity while restricting high-risk data movement across SaaS and web apps.
- Prove Hybrid Data Control: Show leadership exactly how policy enforcement persists on and off the corporate network.

Featured resources for securing hybrid work
FAQ: data protection for hybrid workers
We scan and govern the prompts and data being sent to generative AI platforms in real-time. This allows you to set policies that block sensitive information, like PII or intellectual property, from being uploaded, ensuring your teams can innovate without creating new risks.
Yes. Our protection is centered on the endpoint, not the network. Policies are enforced directly on the device, so your data remains secure whether an employee is in the office, at home, or connected to public Wi-Fi.
Traditional DLPs are blind once a device leaves the corporate network. Our solution lives on the endpoint, providing constant visibility and enforcement. It sees context that network tools miss, like data being moved to a USB drive or copied into an unauthorized application.
No. The endpoint agent is lightweight and designed for minimal performance impact. It runs efficiently in the background, providing robust security without interfering with user productivity or device performance.
Absolutely. We prioritize seamless integration. Our solution is designed to complement your existing security tools, like UEM and EDR platforms, to enhance your overall security posture without requiring a complete overhaul of your tech stack.
