Prove Compliance On Demand—Or Risk Exposure

The problem
When audits and security controls fail, consequences are immediate: regulatory penalties, sensitive data exposure, and lost trust. Many enterprises still rely on manual checks, disconnected tools, and reactive remediation across complex frameworks like HIPAA and PCI DSS—creating blind spots that increase outage risk and disrupt business continuity.
Compliance failure becomes business failure
Compliance gaps rarely announce themselves. Encryption lapses quietly. Patches fail silently. Security agents stop reporting. And when auditors—or attackers—find the weakness first, the damage is already done.
Fines can reach €20M. HIPAA settlements regularly hit seven figures. But the real threat is operational paralysis. Downtime exceeding $1M per hour compounds fast, eroding customer trust and executive confidence. If you can’t prove control effectiveness in real time, you’re gambling with regulatory exposure, outage risk, and brand reputation.
With Absolute, Allina Health saved over $1M, proved HIPAA compliance by validating encryption on all devices at all times, and achieved 95% laptop auditing accuracy.
Enforce continuous compliance without chaos
Absolute Security transforms compliance from a periodic fire drill into a continuous, automated state.
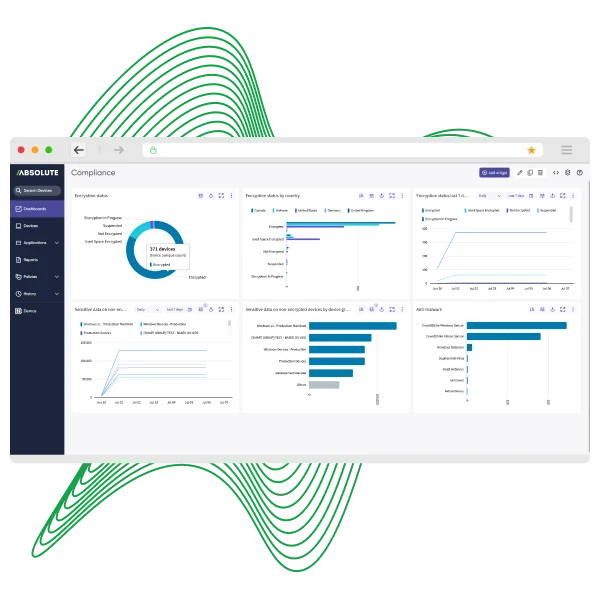
The unified cyber resilience platform verifies encryption, enforces patching and configuration baselines, self-heals failed security controls, and delivers real-time dashboards with exportable audit-ready reporting. Instead of scrambling before audits, organizations can prove regulatory alignment anytime—while reducing outage risk and strengthening operational resilience.
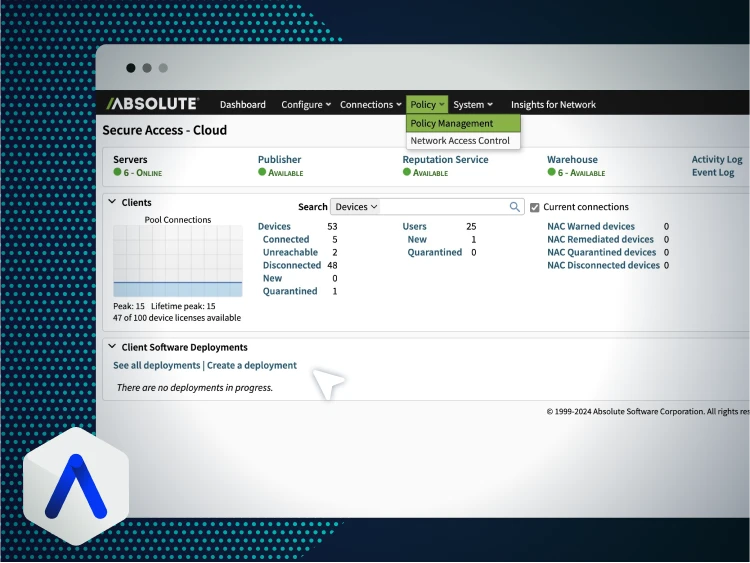
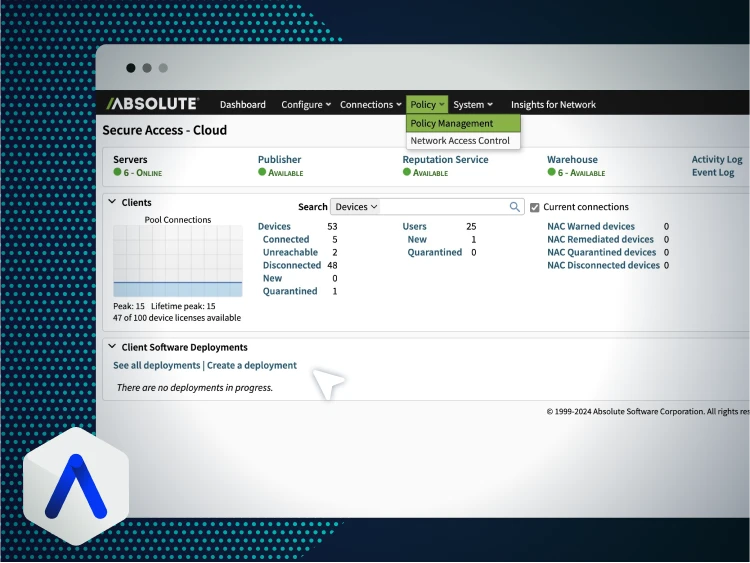
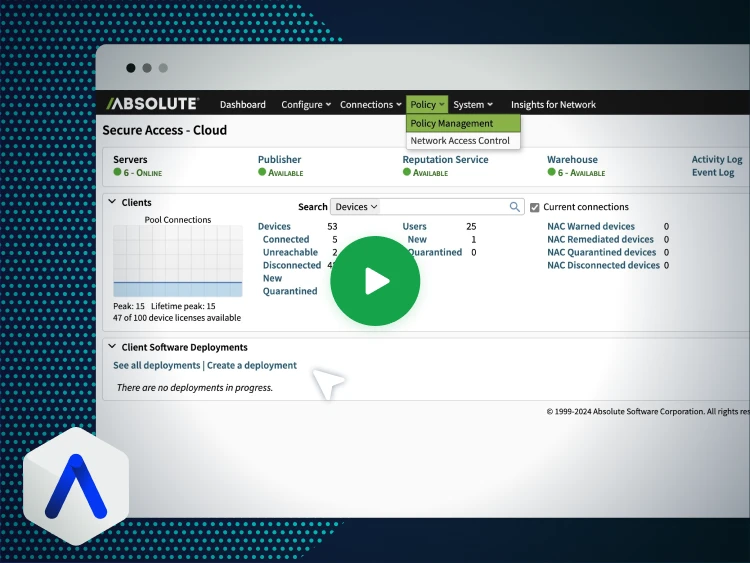
See continuous compliance enforcement in action
Discover how endpoint resilience and Zero Trust access policies automate enforcement, maintain encryption, and generate audit-ready evidence in real time.
- Required Applications policies keep controls running
- ZTNA enforcement based on real-time device posture
- Real-time dashboards and exportable audit reports


Compliance at scale with Genpact
Genpact faced rising compliance risks across 30 countries during a global remote work transition. Using Absolute Secure Endpoint, the organization achieved full visibility across more than 50,000 PCs while maintaining regulatory alignment.
By leveraging firmware-embedded persistence and self-healing controls, Genpact reduced compliance defects by 50%, demonstrating how resilience directly drives audit readiness at scale.
- Mobilized 50,000+ PCs globally while maintaining compliance
- Reduced compliance defects by 50%
- Achieved full endpoint visibility across 30 countries
Key capabilities for continuous compliance enforcement
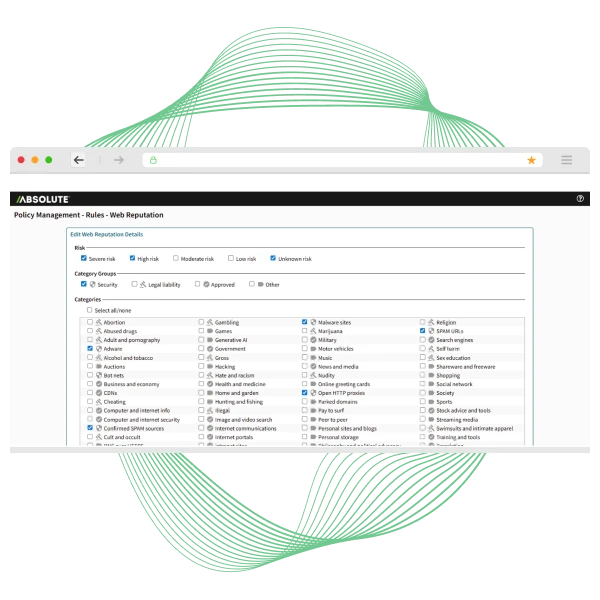
Automated OS and third-party patching, configuration baseline enforcement, drift remediation, and encryption verification.
Ensure critical security apps stay installed and operational to prevent outages caused by failed controls.
Dynamic ZTNA policies enforce least-privilege access based on real-time device and user context.
Gain visibility into SaaS usage and govern unsanctioned applications and rogue AI tools.
Protect sensitive data from exfiltration with granular controls and remote browser isolation.
Real-time dashboards and exportable reports mapped to frameworks including HIPAA, GDPR, CJIS, and PCI DSS.
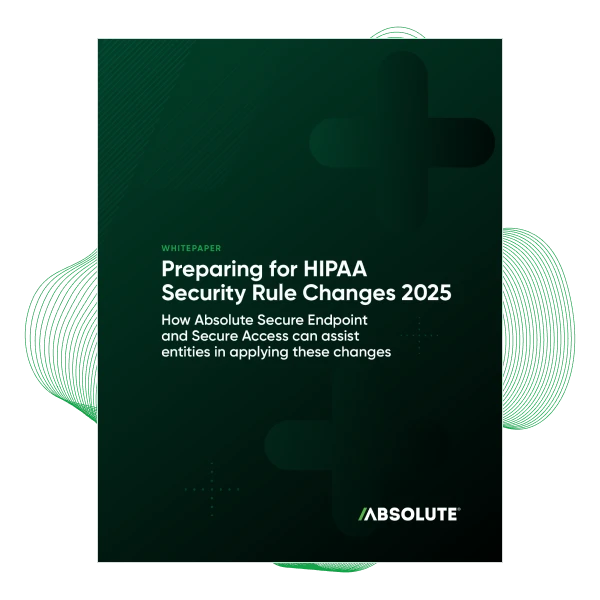
Prepare for 2026 HIPAA security changes
Significant HIPAA updates are coming in 2026, introducing mandatory encryption, MFA, and expanded risk analysis requirements. This whitepaper provides practical guidance to help organizations prepare proactively.
Inside you’ll learn:
- New encryption and MFA mandates
- Annual asset inventory expectations
- How Zero Trust strengthens HIPAA alignment
- Steps to enhance resilience while accelerating compliance
See compliance gaps before auditors do
Discover how to gain instant visibility into your compliance posture and uncover risks before they become audit findings. Absolute provides continuous enforcement, posture validation, and audit-ready reporting across endpoint and access controls.
- Assess posture against HIPAA, GDPR, and NIST
- Define and test custom compliance policies
- Export real-time dashboards and reports
More resources on continuous compliance & risk mitigation
Continuous compliance & audit readiness FAQs
You define patching rules that deploy automatically across endpoints. Compliance status is continuously tracked with detailed reporting aligned to regulatory frameworks.
Yes. Commands and policies are delivered to devices even if rarely online or operating on unstable connections.
AI-driven insights help identify non-compliant devices, detect zero-day risks, and surface shadow AI usage for remediation.
Real-time dashboards and customizable reports provide instant visibility into patch levels, encryption status, device configuration, and policy enforcement.
Yes. Absolute strengthens your existing stack by providing persistent visibility and control at the endpoint layer.
