Secure Remote Work With Zero Trust Access

The problem
The perimeter is gone—but organizations still act like it exists. Remote users connect through legacy VPNs that grant broad network access once authenticated, creating unnecessary exposure.
When credentials are compromised, attackers move laterally with ease. Meanwhile, backhauling traffic through centralized choke points frustrates users and slows productivity. The traditional “connect first, secure later” model no longer fits a cloud-first, hybrid workforce.
Clinging to VPNs is expanding your attack surface
Every VPN connection can unlock more access than intended. Broad network permissions create opportunity for lateral movement, especially when credentials are compromised.
As enterprise traffic increasingly bypasses corporate networks, visibility gaps widen. Risky web and SaaS activity often becomes the starting point for data loss. The uncomfortable reality: the tools meant to connect remote teams may now be exposing them.
By working with Absolute, we not only have the ability to ensure all endpoints are secure, protected, and updated, but we also have complete visibility into the status of our device estate. This means we can ensure each and every laptop is fully operational, and that unused devices can be quickly updated and returned for use.
Replace VPN risk with Zero Trust control
Zero Trust Network Access (ZTNA) flips the model. Instead of granting broad network connectivity, access is limited to specific applications based on identity, device posture, and context.
Absolute Secure Access enforces least-privilege, per-application policies that prevent lateral movement and eliminate the risks associated with traditional VPNs. Users get seamless connectivity across any network—HQ, home, or mobile—while IT gains centralized visibility and control.
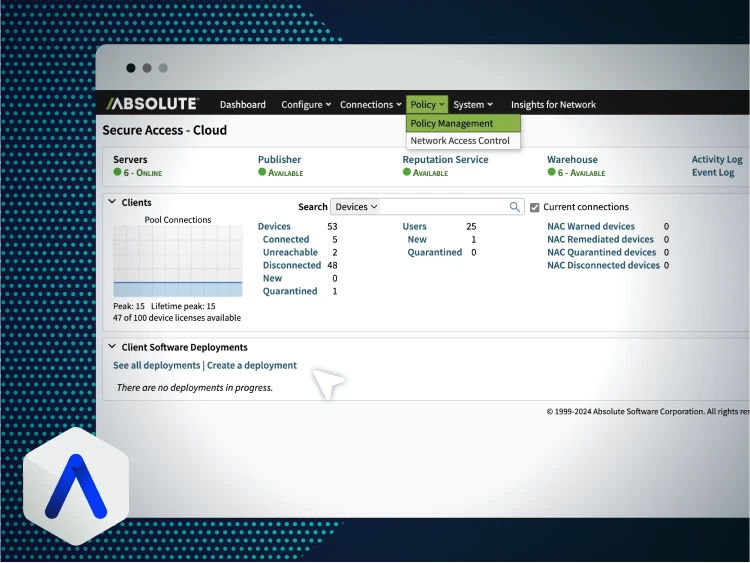
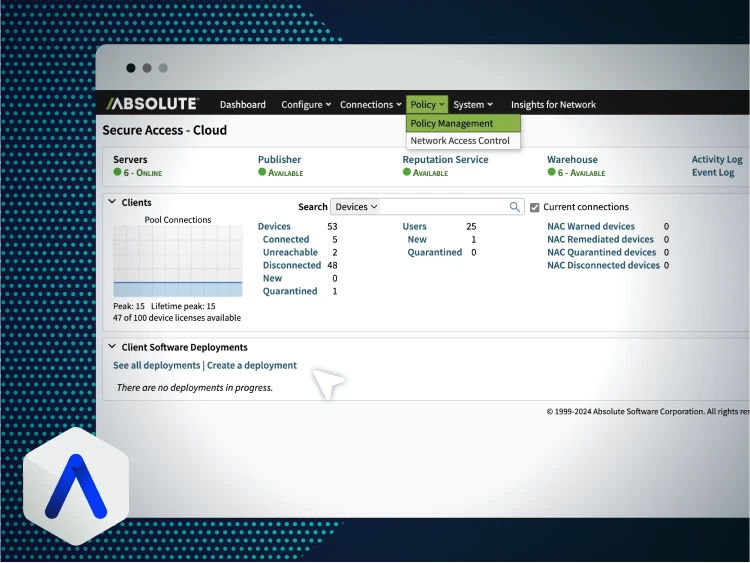
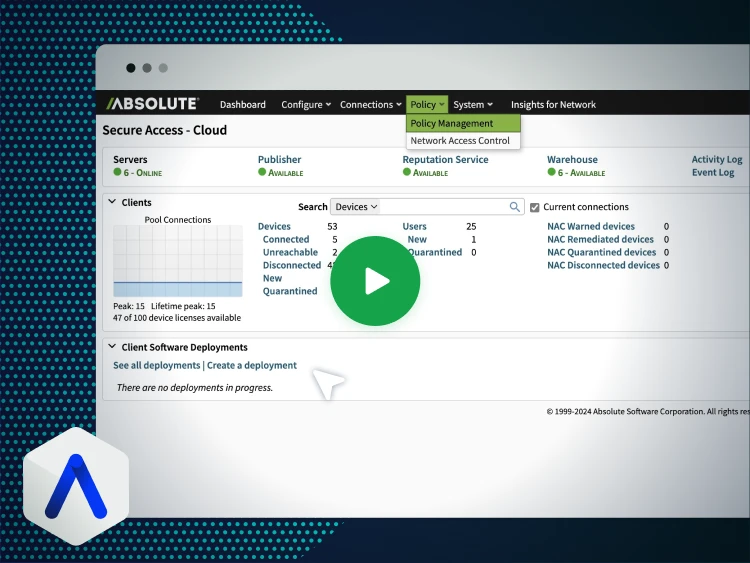
See Zero Trust Network Access in action
Watch how Absolute Secure Access replaces VPN access with resilient, app-level Zero Trust connectivity—without slowing users down.
- Cloak infrastructure from the public internet
- Enforce posture-based, per-app access policies
- Maintain seamless sessions during network switching


Keeping critical NHS staff securely connected
NHS Norfolk Community Trust transformed unreliable mobile connections into a secure, resilient lifeline for 800 nurses and 2,000 staff.
With Absolute Secure Access, the organization reduced incident reports and ensured uninterrupted access to critical systems. Zero Trust enforcement and always-on connectivity allowed vital healthcare services to remain available—even during mobile network dropouts.
- 99% fewer connectivity issues
- Always-on Secure Access during mobile dropouts
- Improved productivity for clinical staff
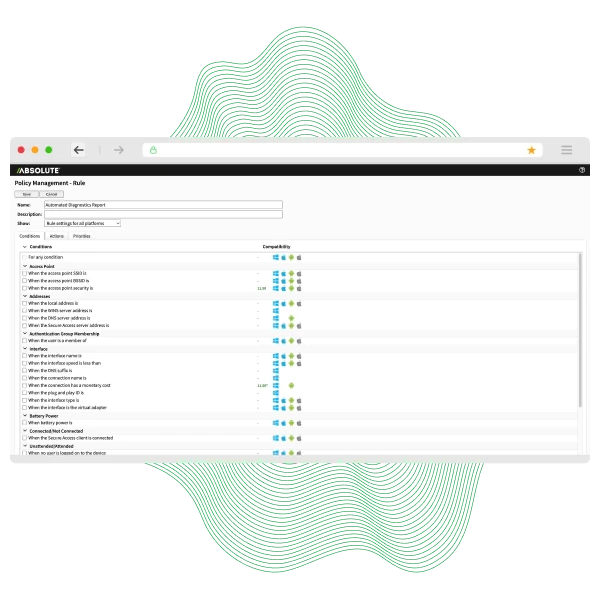
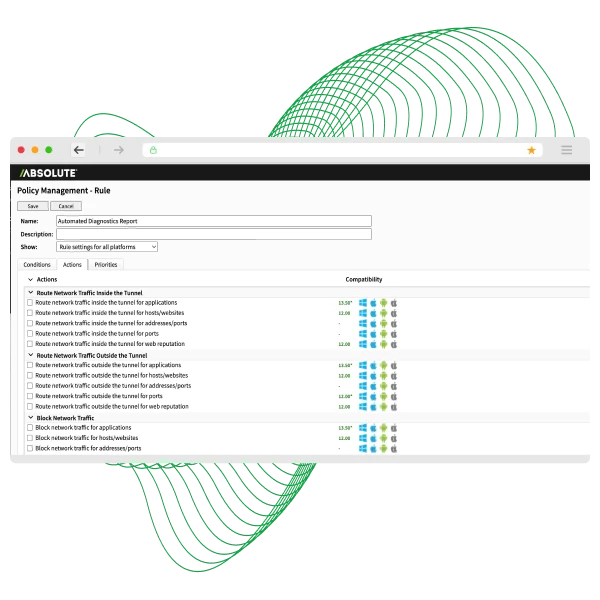
Key capabilities for modern Zero Trust access
Enforce least-privilege, per-app access. Users only see what they are authorized to use.
Eliminate lateral movement by restricting access at the application layer—not the network.
Verify device encryption, OS version, and anti-malware status before granting access.
Integrate with SSO and MFA providers to tie access strictly to verified user identity.
Handle packet loss, jitter, and network switching seamlessly to prevent session drops.
Maintain consistent enforcement with real-time visibility into access attempts and compliance.
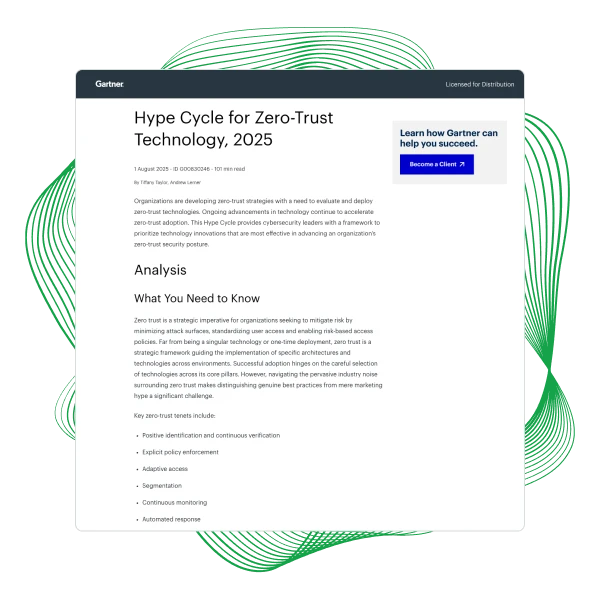
Recognized in the 2025 Hype Cycle™ for Zero Trust
Gartner recognized Absolute in the 2025 Hype Cycle™ for Zero-Trust Technology. This research explores why resilience is becoming foundational to modern Zero Trust strategies.
Inside you’ll learn:
- Which Zero Trust technologies matter most
- Why resilience strengthens ZTNA effectiveness
- How to close the gap between policy and enforcement
- Where traditional VPN approaches fall short
Ready to replace your VPN?
Stop relying on legacy VPN models that expand access beyond what users need. Secure remote work with resilient Zero Trust Network Access that enforces least privilege, reduces lateral movement, and keeps teams productive anywhere.
- Replace VPN with app-level access
- Enforce policy based on identity and posture
- Deliver seamless connectivity across networks
More resources on secure remote access & ZTNA
Zero Trust remote access FAQs
Yes. Secure Access replaces broad network VPN connectivity with granular, identity-driven ZTNA policies.
The resilient tunnel maintains sessions during packet loss, jitter, or network switching, preventing re-authentication loops.
Yes. Policies verify encryption, patch status, and endpoint protection before granting access.
No. The client can be deployed silently through standard device management tools and centrally managed.
Yes. Web-based access options and specific policies enable secure third-party or unmanaged device access.
