Stop SaaS Sprawl Before It Stops You

The problem
Shadow IT, unsanctioned SaaS, and unchecked AI tools have quietly reshaped your threat surface. Employees adopt cloud apps and generative AI platforms beyond the reach of traditional controls—moving regulated data through browsers, plugins, and personal tenants.
Legacy gateways and network-based CASBs lose visibility the moment traffic bypasses the perimeter. Sensitive uploads, public cloud shares, and Shadow AI usage slip through unnoticed—until the breach, audit finding, or fine makes it visible.
When SaaS runs wild, risk multiplies fast
Every unmanaged SaaS app increases your attack surface. Personal logins to corporate platforms enable silent data exfiltration. AI plugins introduce unknown processing paths for regulated data.
Unauthorized cloud and AI usage isn’t just policy drift—it’s exposure to data loss, compliance penalties, and operational disruption that compounds with every off-network session.
Most CISOs and IT leaders agree that generative AI use is expanding, with Shadow AI adding unknown risks. One leading analyst organization predicts that a majority of workers will soon ignore their organizations’ security policies and use an AI platform of their choice to perform tasks.
Enforce policies where risk actually happens
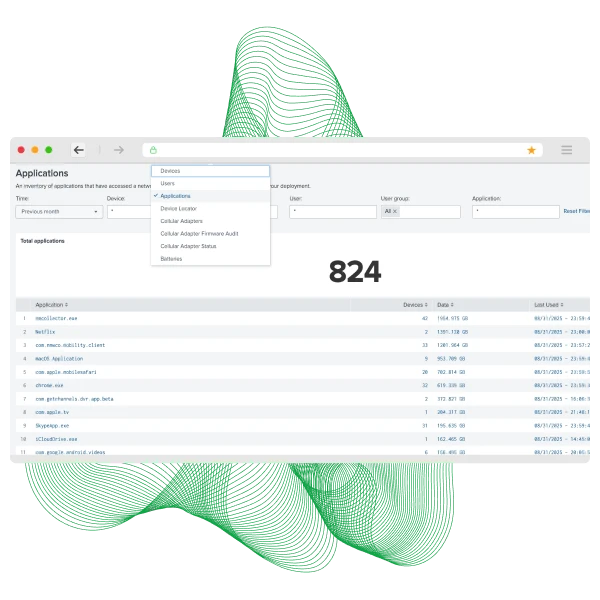
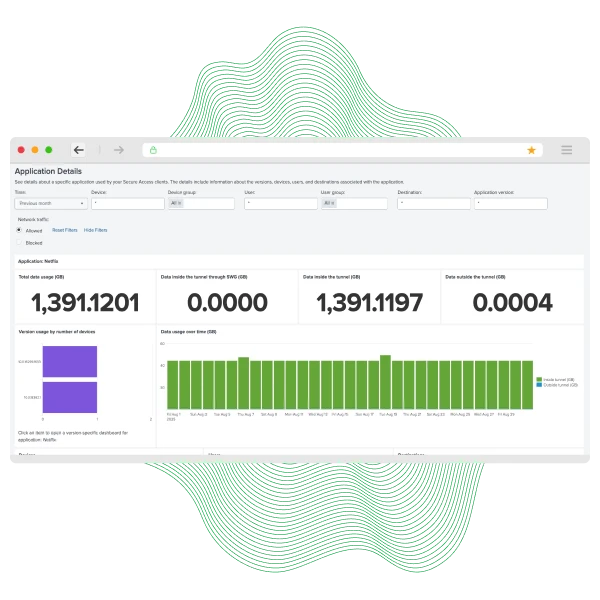
Absolute Secure Web & SaaS Access applies inline SWG and CASB controls with endpoint enforcement—so policy doesn’t disappear when users leave the corporate network.
Gain tenant-level control, block personal SaaS logins, govern uploads and shares, detect Shadow IT and Shadow AI, and maintain session integrity across any network. Security follows the device, not the perimeter—preserving productivity without sacrificing control.
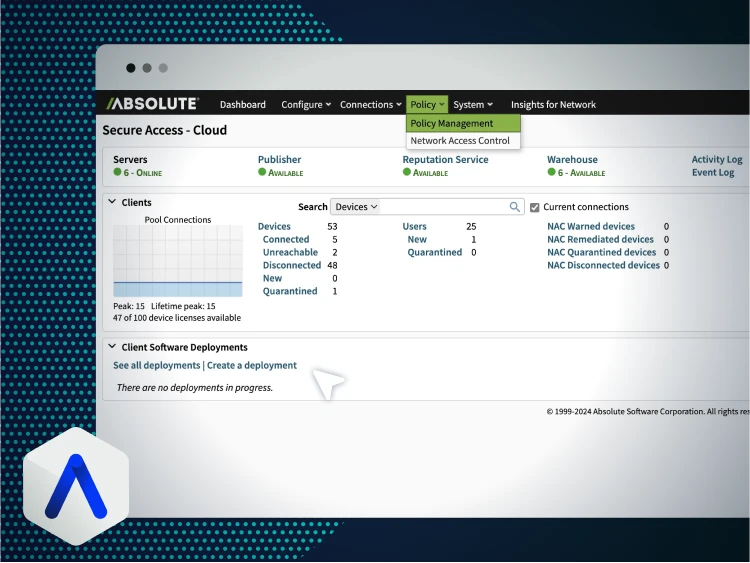
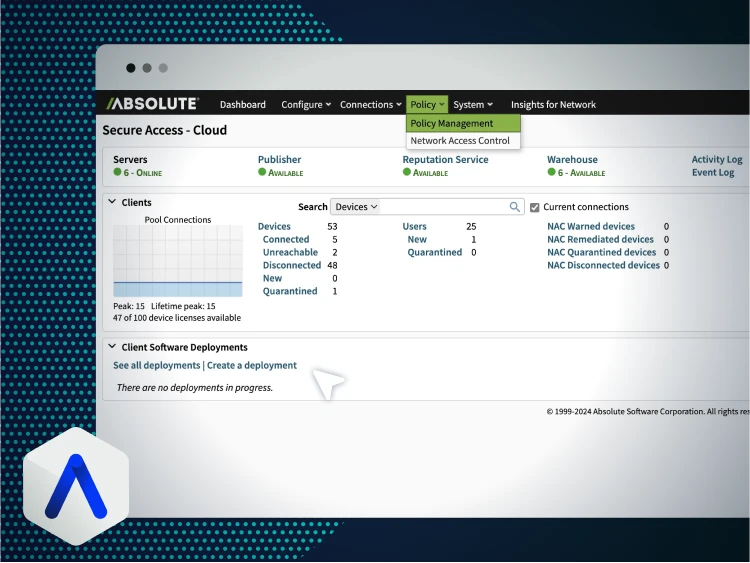
See real-time SaaS policy enforcement in action
Watch secure SaaS access persist across network switching, tenant controls, and real-time traffic inspection—without session drops or re-authentication loops.
- Live network switching with zero session loss
- Tenant control blocking personal SaaS logins
- Real-time traffic prioritization for business apps



Aviation-grade secure SaaS access at scale
Air Corsica modernized remote and cloud access with Absolute Secure Access, delivering resilient, compliant connectivity across EMEA aviation operations.
The organization achieved continuous secure SaaS access with self-healing VPN, ZTNA-ready architecture, and unified policy enforcement—ensuring productivity and regulatory compliance in a highly regulated environment.
- Continuous secure SaaS access across aviation teams
- Stronger DGAC compliance with unified remote access
- Zero Trust foundation across hundreds of endpoints
Key capabilities for secure web & SaaS control
Inspect web and SaaS traffic in real time. Block risky destinations and enforce policy across any network.
Allow corporate tenants only. Block personal Microsoft 365 or Google Workspace logins to prevent data exfiltration.
Detect unsanctioned SaaS and AI tools. Apply policy instantly to reduce unknown exposure.
Security lives on the device. Protection persists on or off network—even offline.
Allow downloads but block uploads by data type, user role, or context.
Isolate risky sessions and automatically sanitize downloads to keep endpoints clean.
Why CISOs are prioritizing resilient secure access
The State of Enterprise Cyber Resilience report, based on insights from 750 CISOs globally, reveals why secure web and SaaS access is becoming foundational to enterprise continuity.
Inside you’ll learn:
- Why resilience now outranks legacy prevention
- How CISOs are redefining secure access strategy
- Why self-healing secure SaaS access matters
- What Zero Trust looks like in practice
Take back control of your SaaS risk
Secure SaaS access can’t rely on network boundaries that no longer exist. Absolute enforces policy at the endpoint—governing Shadow IT, Shadow AI, tenant access, and data movement wherever work happens.
- Block personal SaaS accounts instantly
- Govern uploads and AI usage in real time
- Maintain secure sessions across any network
More resources on secure web & SaaS access
Secure web & SaaS access FAQs
It can, but it also enhances it. Absolute integrates CASB functionality with endpoint enforcement, covering gaps when users go off-network.
Yes. Tenant control allows corporate logins while blocking personal accounts on the same device.
Traditional SWGs rely on traffic flowing through a gateway. Absolute enforces policies directly at the endpoint—even when traffic bypasses the network.
You gain visibility into AI platforms and plugins in use and can block, isolate, or govern them based on policy.
Yes. Endpoint-enforced policies remain active even without internet connectivity.
No. Because Absolute technology is embedded in the firmware of most enterprise PCs, activation is streamlined and fast.
Yes. Policies allow granular control—download permitted, upload restricted—based on context and sensitivity.
