Unify Device Health and Access to Stop Downtime
Resilience Without Disruption: Powering Continuous Operations
Cyber incidents are inevitable. Downtime should not be. For security leaders, success is no longer defined by prevention alone, but by the ability to stay operational and recover fast. The ability to anticipate, withstand, recover, and adapt to disruptions dictates whether an organization thrives or stalls.
When a breach occurs, the questions from the board are immediate: Are we still operational? How quickly can we recover? Can we maintain trust?
Answering these questions confidently requires more than fragmented security tools. It requires a permanent digital connection to every endpoint, ensuring they remain visible, protected, and compliant always. This is why we created Absolute Ultimate.
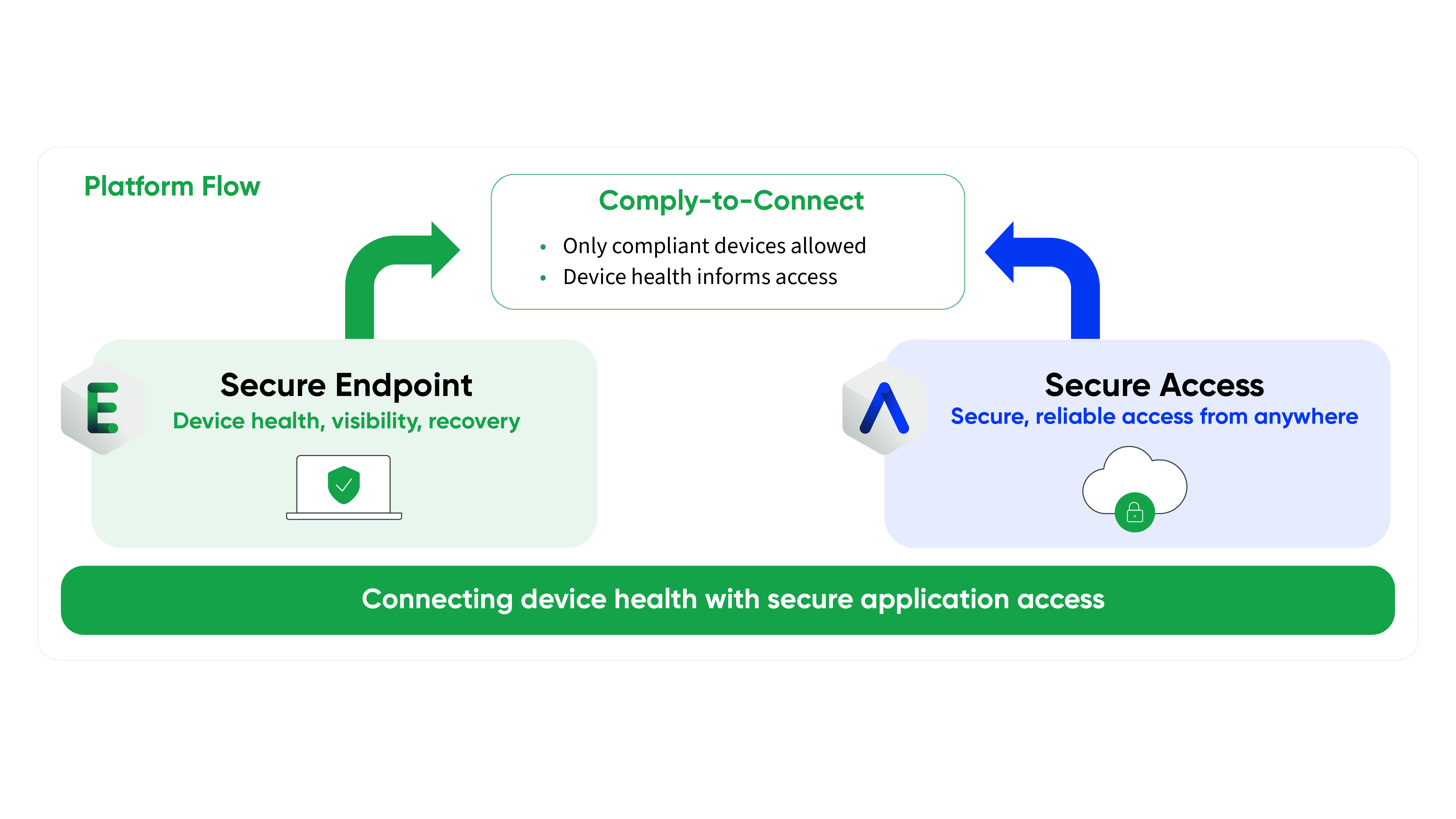
By combining the power of Absolute Secure Endpoint and Absolute Secure Access, Absolute Ultimate delivers an unbreakable connection that unifies device health with secure, resilient connectivity.
The Strategic Imperative of Operational Resilience
Resilience determines how quickly you get back to business. Yet, many organizations struggle to maintain sustained control during disruption. When an endpoint is compromised, traditional software-based security agents are often the first things disabled by attackers. Lose visibility into the device, and you lose the ability to respond.
Security success is measured by uptime, recovery, and productivity. You need assurance that your security controls remain active and enforceable, even when devices are compromised, replaced, or reimaged.
Why Fragmented Tooling Creates Blind Spots
Managing cyber risk across a distributed, hybrid environment requires simplicity. Tool sprawl introduces friction, operational complexity, and critical blind spots. Security teams are overwhelmed with alerts, while executives lack a clear, defensible view of the organization's actual risk posture.
Relying on separate solutions for endpoint visibility and secure network access creates gaps. Devices might connect to corporate resources without a verified health check. Alternatively, endpoints might be visible but lack the secure, optimized tunnels needed for employees to work effectively from anywhere.
To achieve measurable resilience, endpoint, access, and application security must work together.
Absolute Ultimate: Secure Endpoint Meets Secure Access
Absolute Ultimate is the only purpose-built solution for true enterprise cyber resilience. Factory-embedded in more than 600 million endpoints, Absolute provides a permanent digital connection that dynamically applies visibility, control, and self-healing capabilities to endpoints, applications, and network connections.
By merging Secure Endpoint and Secure Access, Absolute Ultimate empowers organizations to maintain operational continuity regardless of the circumstances.
Sustained Control During Active Disruption
With Absolute Ultimate, you create an unbreakable connection to your fleet. This firmware-embedded persistence ensures that if your core security agents—like anti-malware or encryption—are disabled or corrupted, they automatically self-heal and reinstall.
At the same time, Secure Access guarantees that users enjoy resilient, optimized, and secure network connections. If a connection drops or transitions between networks, the tunnel persists. This keeps organizations operational, productive, and secure without frustrating the workforce.
Verify Device Health Before Granting Access
Risk management requires continuous verification. Absolute Ultimate’s Comply to Connect solution allows you to assess the deep health and compliance of a device before granting it access to corporate resources. You can enforce policies that mandate specific security controls are running and fully functional. If a device falls out of compliance, you can dynamically restrict access or trigger automated remediation to restore the device to a trusted state.
Executive-Ready Security Outcomes
CISOs need security controls that translate into clear, defensible outcomes. Absolute Ultimate simplifies your security architecture while providing the precise data needed for executive leadership, auditors, and the board.
- Reduced Business Disruption: Stop disruption in minutes, not hours or days. Automatically restore devices, applications, and access to a trusted, compliant state.
- Proactive Risk Management: Gain comprehensive visibility into your entire hardware and software inventory to identify vulnerabilities before they are exploited.
- Defensible Compliance: Generate clear, accurate reports demonstrating continuous compliance with industry regulations and internal policies.
This is risk reduction with measurable resilience. It provides the assurance needed to confidently report on your security posture and operational readiness.
Accelerate Your Resilience Strategy
Whether you are an existing Absolute Secure Endpoint customer looking to add robust access controls, a Secure Access customer needing deeper device visibility, or a new prospect evaluating a unified resilience platform, now is the time to act.
We are on a mission to help organizations strengthen cyber resiliency. To support this approach, we are offering a unique opportunity to experience the comprehensive benefits of Absolute Ultimate.
For a limited time, you can receive the first 90 days free when you purchase a one-year license of Absolute Ultimate.
This enables organizations to elevate your security posture, reduce risk, and demonstrate concrete ROI to your leadership team without impacting your immediate budget cycle.
Please note: This offer is available until June 30, 2026.
Secure Your Future Today
The future of cybersecurity is resilience—always-on control from firmware to cloud, enabling rapid recovery to a trusted state. Do not wait for the next disruption to test your continuity plans.
Equip your organization with the only enterprise resilience platform that ensures you are always on, always connected, and always protected. Take advantage of our current promotion to unify your device health and secure access strategies.
Contact our team today to claim your first 90 days free and start building a board-ready security posture that keeps your business moving forward.
To learn more, check out the following data sheet and view the product tours.