Stop Chasing Alerts. Start Preventing Breaches.

The problem
The endless barrage of security alerts and logs has created an illusion of control but hasn't truly closed the gap on emerging threats. Relying on visibility alone, without proactive intervention, means you're just chronicling attacks instead of stopping them. Truly effective threat detection and prevention go beyond watching and logging; they intercept malicious activity before damage occurs. If your security strategy rests on digging through noisy alerts to find actual threats, you're not protecting your organization—you're just keeping records for the aftermath.
When "detect and respond" is too late
The focus on reaction leaves a dangerous gap where threats can fester. It’s not just a matter of lost dollars: operational chaos and eroded trust come right on their heels. Human error still drives most breaches: nearly three-quarters involve some form of user action, like a single click on a phishing link. Ransomware isn’t just a bullet point on a board slide; it can cost organizations over $5 million per incident, often through nothing more than a crafted malicious file or an innocent-looking URL. And vulnerabilities don’t wait for manual patch cycles, breaches caused by exploiting known weaknesses have soared by 180% year over year.
Telemetry is a double-edged sword. It is critical to establishing effective defences that can detect and stop threats and bad behaviours, but it can also lead to overwhelming false alarms that destroy productivity and lead to missed events.
Get ahead of the attack
True threat prevention isn’t about building higher walls; it’s about neutralizing threats mid-air, before they ever touch your endpoints. We shift the focus from reaction to proactive prevention. This starts by inspecting web traffic in real time and isolating risk before it becomes an incident.
By combining inline web inspection, Remote Browser Isolation (RBI), and Content Disarm & Reconstruction (CDR), you create a buffer between users and the internet. Risky browsing sessions are executed in a disposable cloud container. Weaponized files are stripped of malicious code before they are downloaded. This isn't just another layer of defense; it's an active, intelligent system that assumes all inbound content is suspect until proven safe.
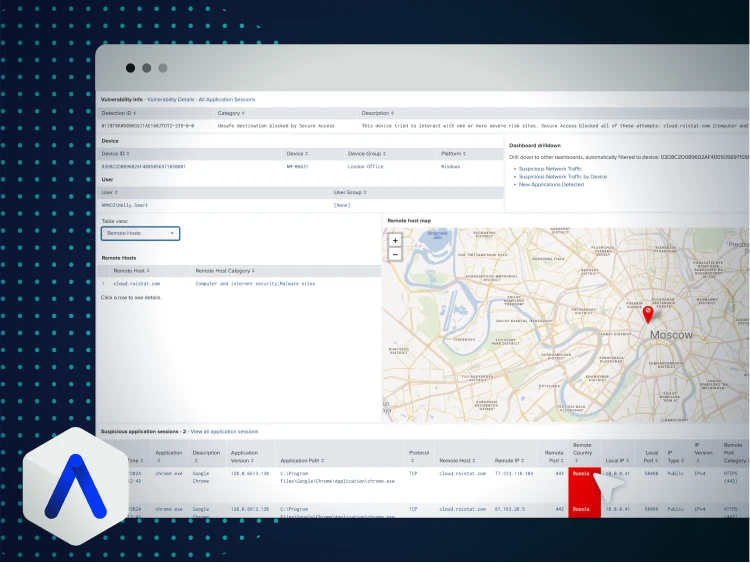
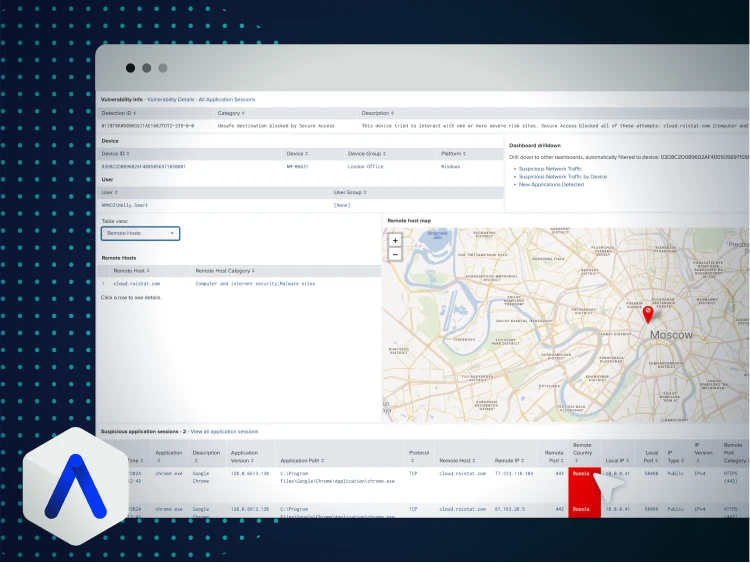
Pinpoint threats without the noise. And deal with them.
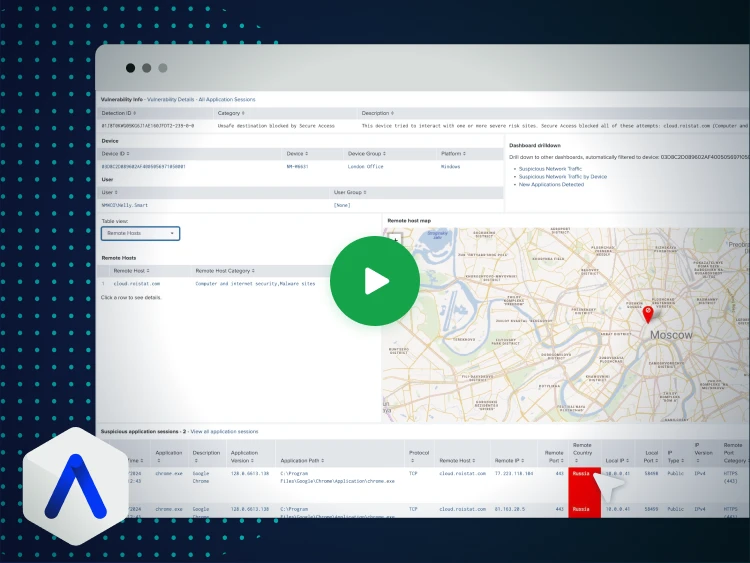
Identify threats and respond faster with Absolute Security. Cut through noise and stop attacks before they start. Take the tour to see AI-powered insights in action.
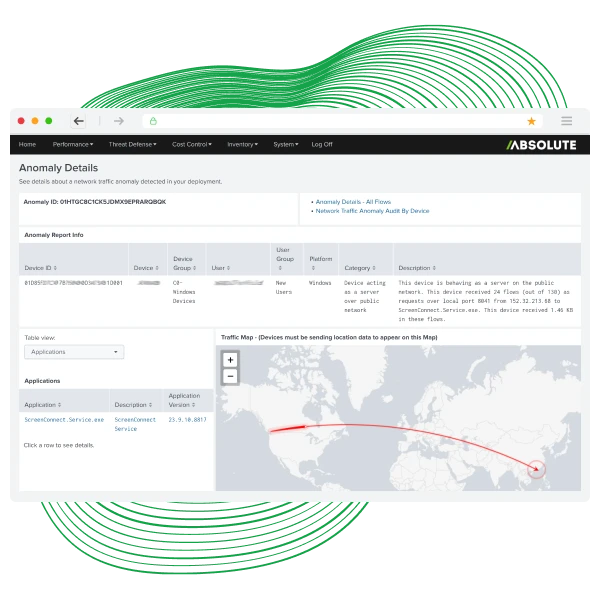
- Detect zero-day threats instantly with AI and ML monitoring for behaviors, data exfiltration, and atypical app usage.
- Act fast with proactive alerts that prioritize vulnerabilities using your organization’s own data—never aggregated sources.


Rock‑solid defense for every device
Osborne Clarke struggled with visibility and unstable connectivity as lawyers worked across 25 global locations. Absolute delivered real‑time insight into device, app, and network behavior, helping the firm detect issues faster and keep users securely connected.
- Deep Visibility: Pinpoints device, app, and network issues early to reduce blind spots.
- Secure, Stable Access: Zero Trust connectivity that prevents dropouts and protects firm resources.
- Fewer Disruptions: Fee earners stay productive with consistent, threat resilient access.
Core capabilities for threat detection and prevention
- Inline Inspection & Malware Protection
- Remote Browser Isolation (RBI)
- Content Disarm & Reconstruction (CDR)
- AI-Powered Threat Insights
- User and Entity Behavior Analytics (UEBA)
- Proactive Vulnerability Prioritization
- Distributed Firewall Policy
- Command-and-Control (C2C) Blocking
- Network Access Control (NAC)
- Self-Healing Controls
Mitigating zero-day threats in a complex environments
Discover how to protect your workforce from sophisticated cyberattacks—without adding complexity. Watch our on-demand webinar, Mitigating Zero-Day Threats in a Complex Cybersecurity Landscape, and learn how to:
- Stop Zero-Day Exploits: Leverage Remote Browser Isolation (RBI) and Content Disarm & Reconstruction (CDR) to neutralize threats before they strike.
- Safeguard Sensitive Data: Prevent data leaks and ensure compliance with built-in Data Loss Prevention (DLP).

See threat protection live: book a demo
Ready to stop zero-day attacks before they start? Experience how Absolute Secure Access delivers resilient, AI-powered threat prevention for your hybrid workforce.
Why request a live demo?
- Multi-layered defense: See advanced techniques like Remote Browser Isolation (RBI) and Content Disarm & Reconstruction (CDR) neutralize zero-day threats without slowing users down.
- AI-driven insights: Watch how ML-based UEBA detects suspicious behaviors in real time—before they become breaches.

Featured resources for threat protection and prevention
FAQ: your threat protection questions answered
Standard SWGs mostly block known malicious domains. Attackers know this and develop novel tactics that evade these lists. That’s why we combine SWG features with Remote Browser Isolation (RBI)—so even if a threat is totally new, risky sessions are isolated in the cloud and never touch your endpoints. Content Disarm & Reconstruction (CDR) takes it further, scrubbing potentially weaponized files before delivery. The combination covers both the known and the unknown, reducing gaps attackers exploit.
Access controls, threat inspection, and policy enforcement happen directly on each endpoint—no dependency on the corporate network or VPN. Whether users are at home, in a coffee shop, or in another country, their devices are governed by the same Zero Trust rules. Secure Access features, like device posture checks and granular, least-privilege ZTNA enforcement, extend protection everywhere your work goes.
Frankly, if security gets in the way, users find workarounds—and that’s a risk on its own. Here, performance and experience matter. RBI only isolates risky browsing; trusted sites operate at normal speed. Automated patching, remediation, and policy changes happen in the background. The result? Users stay efficient while risk is managed behind the scenes.
EDR shines at detection and response after a breach. Our approach focuses on prevention—blocking threats in web traffic, hardening devices, and maintaining application health before bad actors get a shot. Malware that never lands, alerts that never trigger, and vulnerabilities that never open the door. In practice, this means less alert fatigue for security teams and better ROI from every security tool.
You get detailed metrics: the number of blocked threats in real time, sanitized files delivered, vulnerabilities patched automatically, devices remediated, and non-compliant endpoints brought into line. Track reduced incident rates, lower MTTR, improved compliance, and savings from automation. When the board asks, “Is this working?” you’ll have hard evidence, not wishful thinking.
Deployment is streamlined. Secure Endpoint’s persistent agent activates with a few clicks and immediately starts reporting device health and enforcing controls—even if machines are off the VPN. Secure Access integrates ZTNA and RBI via lightweight connectors or agents, providing granular policy control and inline inspections from Day 1. Integration with existing identity providers and UEM/MDM platforms means you won’t have to rebuild your stack to get these benefits.
ZTNA is the connective tissue for all of this. Every access request is verified—user identity, device compliance, and risk status are checked in real time. Only authorized, healthy endpoints get the minimum access required, and nothing else. This slams the door on lateral movement and privilege escalation, whether users are on-site or anywhere else in the world.
