Stop downtime in your energy and utility field operations




The problem
Field crews are the backbone of energy and utilities—a lost laptop or network outage can trigger a crisis in minutes. Unreliable cellular coverage, outdated VPNs, and a lack of real-time device visibility put productivity, service quality, and data security at risk. Too often, teams rely on hope that devices are safe, connected, and not hiding audit surprises.
Pen and paper workarounds are not a solution
Dropped sessions stall work orders, frustrate field crews, and overflow IT with help desk calls. The risks go deeper: critical SCADA and GIS data may sit unsecured on devices in remote locations. Without real-time visibility and control of every endpoint, your operations, compliance, and data security are always at risk.
Our rural environment had employees re-starting their connections all the time. This caused a lot of extra cycles and delays in service.
Keep your business switched on and flowing
Absolute Secure Access and Absolute Secure Endpoint empower energy and utility organizations to reduce operational risk, minimize downtime, and support field teams with uninterrupted access to mission-critical software. Persistent connectivity, Zero Trust Network Access (ZTNA), comprehensive device visibility, and self-healing security controls work together to maintain compliance, safeguard operations, and ensure productivity—even in the most demanding conditions.
Reliable access to keep the lights — and everything else — on
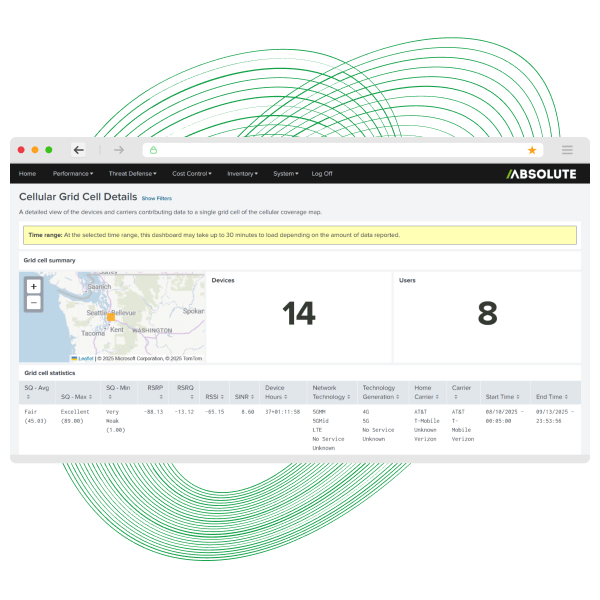
Keep your workforce productive and your critical infrastructure resilient with real‑time visibility across every device, user, app, and network. Absolute Insights for Network helps you spot anomalies fast, troubleshoot, and maintain operational continuity.
- Diagnose issues before outages hit with 70+ dashboards exposing performance, user behavior, and risky network patterns.
- Strengthen cyberresilience across distributed assets with deep insight into device health, app performance, and connectivity.



Reliable access that keeps field crews moving
See how 4-County Electric eliminated dead‑zone dropouts, slashed IT tickets, and kept linemen productive with always‑on connectivity. This case study shows how Absolute Secure Access turns every service vehicle into a fully functioning mobile office—no extra steps, no training, no frustration.
- Dead‑zone downtime stopped with seamless, all‑day connectivity that “just works.”
- Service speed boosted and support tickets cut by giving crews reliable access to every app they depend on.
Essential capabilities for critical infrastructure providers
- Always-on VPN alternative
- Zero trust network access
- Keep field workers online
- Access critical apps
- Enforce antivirus & encryption
- Prevent unauthorized changes
- Find & isolate at-risk devices
- Self-healing security apps
- NERC CIP & SOX support
- Automated compliance checks
- Remediate drifting agents
- Audit-ready reporting
- Isolate breached devices
- Remotely lock or wipe
- Investigate with forensics
- Accelerate mean time to repair
- Endpoint & app automation
- Zero-day fixes
- Integrate with SIEM/SOAR
- Automated patch control
- Asset inventory & tracking
- OS & app deployment
- Remote wipe & retire
- Control device refresh
- Persistent connectivity
- Reduce it support tickets
- Reliable app access
- Minimize worker downtime
- Continuously update CMDB
- API-driven data sync
- Accurate endpoint data
- Reduce manual data entry
Reliable access to faster, safer patch automation
See why GigaOm named Absolute a Leader and Outperformer in the 2025 Radar for Patch Management. This independent analyst report breaks down how Absolute Security streamlines patching, shrinks risk, and bridges IT and SecOps—without adding complexity or slowing teams down.
Inside you’ll learn how to:
- Cut risk with smarter automation including staged rollouts, rollback logic, and real‑time health checks.
- Fix drift fast across distributed teams with custom policies and no-code workflows that plug directly into ServiceNow, ConnectWise, and more.

See how resilient access transforms your endpoint security
Get a hands‑on look at how Absolute Security solutions deliver self‑healing security, resilient connectivity, and automated remediation across every device. In this quick demo, you’ll see how IT and security teams cut risk, fix issues faster, and keep workers productive, no matter where they are.
- Experience real‑time visibility and automated response across your entire endpoint fleet.
- Reduce complexity and boost resilience with a platform built to keep critical operations running smoothly.

Featured resources for Utility Professionals
FAQ – Your resilience questions answered
We keep trying to force-fit office technology into extreme field environments. Traditional VPNs simply cannot handle network drops, cellular dead zones, or moving between coverage areas. When a connection drops, the session dies, and your workers lose access to critical dispatch apps. We use Absolute Secure Access to provide persistent connectivity. Instead of dropping the session, the connection seamlessly suspends and resumes the moment a signal returns. It keeps your field workers online without forcing them to constantly log back in.
It may be unfortunate, but if a device is compromised, the first thing a bad actor (or even a frustrated user) does is disable the security agent. If your tracking tool relies on that agent, you are blind. Absolute takes a different approach. We rely on firmware-embedded persistence built directly into the hardware of most devices. Even if the operating system is wiped or the hard drive is replaced, our connection survives. You get uncompromised visibility to track, manage, or lock that asset no matter what happens to it.
With legacy tools, locking down an endpoint meant choking the user experience. But true resilience isn't about blocking everything; it is about keeping the necessary things running. With self-healing technology, we monitor your mission-critical applications, like antivirus, encryption, and VPNs. If they crash, get corrupted, or are maliciously disabled, Absolute Persistence automatically repairs or reinstalls them with zero IT intervention. You reduce IT support tickets and minimize worker downtime simultaneously.
Think about your SCADA environments and the laptops connecting to them. If the endpoint security fails, that laptop becomes a bridge into your most sensitive networks. Our self-healing technology acts as a failsafe. By autonomously restoring broken security apps, we guarantee that your endpoint security enforcement never wavers. You maintain the strict access controls required by CIP standards without relying on human intervention to notice a failure.
Improving resilience and reducing risk requires a critical evaluation of how you grant access. Just because a worker has the right password does not mean their device is safe to let onto the network. We implement Zero Trust Network Access (ZTNA). Instead of granting broad network access, we evaluate the context of the connection and grant access on a strictly per-application basis. If a device lacks the latest OS patch or its antivirus is disabled, you can automatically block it from accessing your sensitive energy grids.
When an incident happens, the knee-jerk reaction is often to shut everything down to stop the spread. That costs money and stops energy from flowing. Instead of a blunt instrument, we use precision. With Absolute Secure Endpoint, you can remotely locate, lock, or wipe a compromised device in near real-time. You can freeze the specific hardware involved in the breach while allowing the rest of your fleet to continue operating normally. This drastically accelerates your Mean Time to Repair while containing the threat.
It’s often tempting to buy a new tool for every new problem, but this can lead to a tangled, unmanageable web of agents that slows down the machine. Consolidating is not just possible; it is necessary for clarity. By leveraging a unified platform that offers visibility, control, and secure access, you strip away the bloat. You get a streamlined device lifecycle management process—from deployment to remote retire—that actually works, giving you more control over your environment with fewer moving parts.
