Absolute for Government
Cyber resilience for your endpoints and cloud to enable your mission critical needs
Strengthen cyber resiliency and compliance posture
With the Executive Order issued by the U.S. Government to improve the nation’s cybersecurity, it is imperative for federal, state and local government agencies to establish cyber resiliency and Zero-Trust architecture to secure their devices, users, network and cloud. In addition, they must also stay ahead of ever-changing regulatory mandates such as NIST CSF, FISMA, CMMC and CDM to maintain compliance and guard against cyberattacks initiated by cybercriminals, nation-states and internal malicious actors.


Absolute Secure Endpoint achieves FedRAMP© Moderate authorization
Absolute Secure Endpoint empowers federal agencies to strengthen cyber resiliency amid increasing threats and IT complexity. Absolute Security has achieved Federal Risk and Authorization Management Program (FedRAMP®) authorization to operate (ATO) at the moderate impact level for its Secure Endpoint solution. This certification highlights Absolute Security’s commitment to cyber resilience and security for federal agencies migrating to the cloud.
Focused on what matters to you
We are committed to providing solutions that meet the unique and evolving needs of public sector agencies

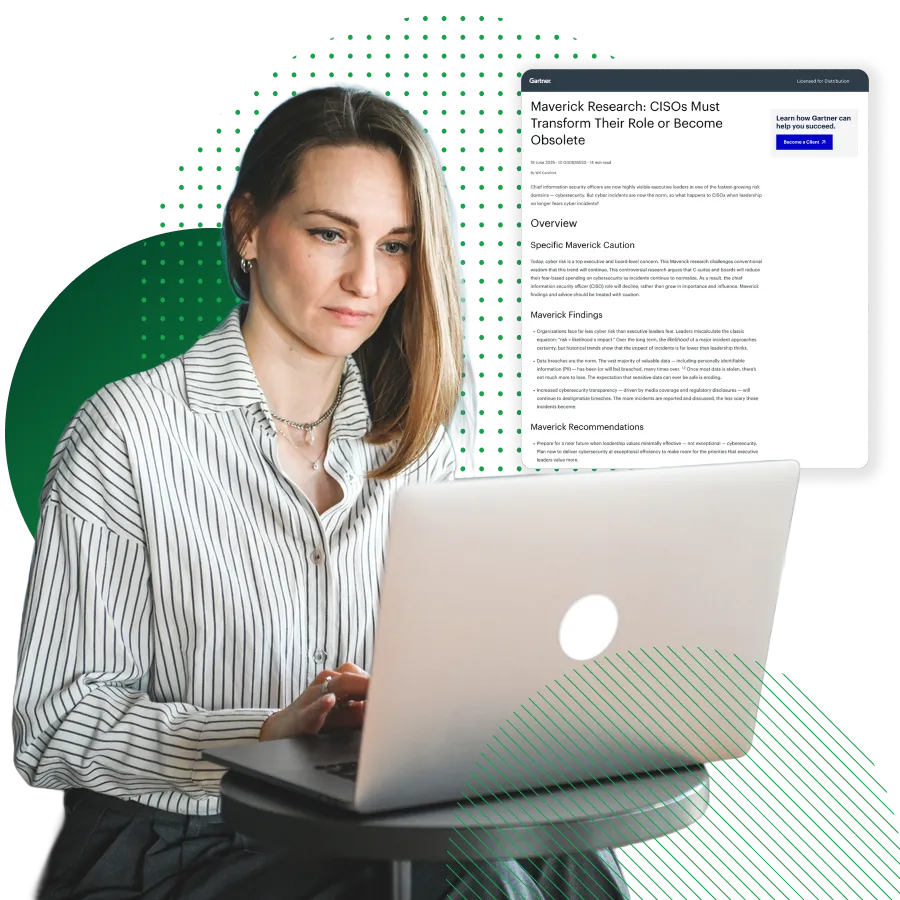
Transform your CISO role from protection to resilience
Evolve your security strategy to deliver value in a new era of cyber risk with Gartner® Maverick research.
Reliable, resilient endpoints
Retain command of all your endpoints, all the time
- Boost your endpoint visibility — on or off your corporate network. Collect hundreds of data points about your devices’ location, security posture, and hardware/software inventory.
- Take advantage of critical control functions such as remote file deletion and data wipe, freezing devices when at-risk, end user messaging, and establishing geo-fences.
- Secure endpoints from threats, respond to security breaches and IT issues through Remote Endpoint Rehydration, and enable Application Resilience to automatically self-heal applications.

Reliable, resilient access
Ensure secure and optimized network access

Government contract vehicles







Featured resources
Like what you're hearing?
Let us show you how Absolute can help keep your devices and sensitive financial data safe and secure