

Few organizations fully recover
from a cyber incident
"Cyber incidents are now a normal — even mundane — occurrence."
"As a result, CISOs must prepare for what senior leadership will want (resilience) over what they once wanted (protection)."
Source: Gartner Research, Maverick Research: CISOs Must Transform Their Role or Become Obsolete, Will Candrick, 19 June 2025.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
annual cost of downtime
(Splunk + Oxford Economics, 2024)
average ransomware/extortion cost
(IBM/Ponemon, 2025)
average data breach cost
(IBM/Ponemon, 2024)
of supply chain breaches are from third-party vulnerabilities
(Verizon DBIR, 2024)
breach cost in shadow AI-heavy organizations
(IBM/Ponemon, 2025)
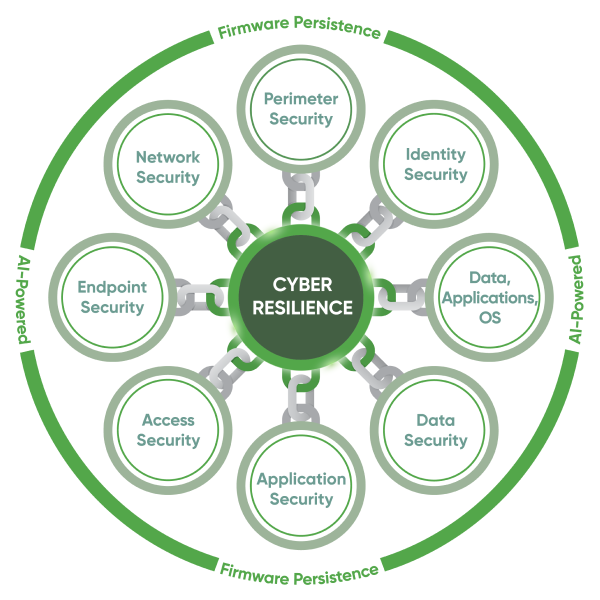
Cybersecurity's Missing Link: RESILIENCE
Security visibility is fragile.
Resilience depends on control that persists through failure, compromise, or isolation.
Resilience is an operational capability, not a security feature.
True recovery demands control that survives OS failure, tampering, or device compromise.
Prevention reduces risk. Resilience keeps the business running.
You can’t stop every attack, but you can recover faster if your security can heal itself.
Real cyber resilience means maintaining control, even when everything else fails – made possible by persistence embedded in the firmware.
The industry's only firmware to cloud platform for endpoints, servers, apps and access
Operates un-deletable at the BIOS level, the only resilience platform you can't remove.
Remotely recovers devices in minutes to a trusted state—not days—without IT delays.
Self-heals before downtime or breaches spread, across endpoints and applications.
Automates patching and vulnerability remediation with 100% control and resilience, for endpoints and servers.
Delivers AI-powered, audit-ready security and compliance with 100% confidence, for CISOs.
30+ years of enterprise
cyber resilience
devices with
Absolute embedded
global
PC OEMs
daily API calls
from endpoints
patents
worldwide
monthly application
health scans


The Absolute Security difference

Persistence
Only Absolute Security's patented persistence technology is embedded in the firmware of over 600 million devices.
Resilience
Only Absolute Security creates an unbreakable connection between device firmware and the Absolute platform.

Intelligence
Only Absolute Security's platform and data uniquely delivers cyber resilience across your entire security stack.

Resilient CISOs and CIOs
rely on us
“Resilience is so important to how you as a CIO or CISO ensure that your organization can weather a breach, ransom attack, or pandemic.”
“I can sleep at night because of Absolute Security. As a CIO, Absolute Secure Endpoint gives me peace of mind. It has strengthened our security posture, allowing us to stay in compliance and giving us that extra level of comfort.”

Resilience Over Protection
The future of cybersecurity requires a bold shift from mere protection to resilience, where CISOs need to transform from being “chief protection officers” into Chief Cyber Resilience Officers. With cyber incidents now an unavoidable and accepted cost of doing business, CISOs’ focus can no longer be on just preventing every attack, but rather on building the ability to anticipate, withstand, adapt, and quickly recover. Modern CISOs understand that the business impact of cyber incidents is the cost of downtime, and by prioritizing resilience, they minimize disruption, maintain continuity, and turn challenges into opportunities.

Recognition, validation,
and certifications

Recognized in Gartner® Hype Cycle™ for Zero-Trust Technology, 2025

Recognized in Forrester Endpoint Management Platforms Landscape, 2025

GigaOm Radar Report Leader, Patch Management Solutions, 2025

GigaOm Radar Report Outperformer, Patch Management Solutions, 2025

Recognized as a Leader in Frost Radar™ for Endpoint Security, 2025

Frost & Sullivan Competitive Strategy & Leadership Award 2025

FedRAMP authorization to operate (ATO)

GovRAMP Authorization at the Moderate level

Certified ISO/IEC 27001
Service Organization Control 2 (SOC2) compliant

Endpoint Management and Zero Trust Networking Leader, Enterprise, G2, Fall 2025

Zero Trust Networking, Enterprise, G2, Fall 2025
Trusted worldwide for
business continuity

of Fortune 500
enterprises

of the top 40 Fortune 500 healthcare providers

of the top 60
global banks








