Embrace a Zero Trust approach
Many organizations have started to embrace a Zero Trust approach and are considering augmenting their conventional network access security concepts such as enterprise virtual private networks (VPNs), with Zero Trust Network Access (ZTNA) solutions. Absolute ZTNA, delivered as part of the Absolute Edge™ product package, stands out in a crowded field.
Highlights

Broad OS support (Windows, Apple iOS and macOS, Android). Resilient Windows client makes optimized tunnel tamper-proof

Minimize risk while optimizing user experience

Allows for continuous real-time risk assessments

Creates a context-based, logical access boundary around a set of applications – wherever they're hosted

Makes applications invisible to unauthorized users, which reduces the attack surface

Resilient, self-healing infrastructure for cloud and on-premises deployment

Optional Secure Web Gateway Service delivers a secure browsing experience for all – desk, mobile, or hybrid users

High performance intelligent client that enforces policy at the endpoint. Seamless user experience across platforms
Absolute AI Threat Insights for proactive alerts!
AI Threat Insights is included with Secure Access Enterprise! Using AI and multidimensional machine learning, it offers proactive alerts of over 50 indicators of suspicious user, device, network, and application activity to IT admins before those issues become problems.

Stay resilient with Absolute ZTNA
Threat detection and prevention
- Ensure uninterrupted secure access, no matter where your employees do their work with the world’s first self-healing ZTNA solution from Absolute.
- The self-healing Secure Access client for Windows can automatically repair or reinstall itself if tampered with, accidentally removed, or otherwise stops working.
- ZTNA policy actions strengthen the foundation of your Zero Trust security posture, bolstering the protection for employees and restricting lateral movement through your network.
- Optionally, scan for the presence of malware, including worms, Trojan horses, and spyware.

Secure and optimized remote access
Secure application access
- Applications are made invisible to unsanctioned users, ensuring your organization is safe from intruders or high-risk connections. Control access to the Web, as well as private and public cloud applications based on risk and compliance requirements associated with a multitude of contextual factors like time of day, user, device’s security posture, geolocation, network connection, etc.
- Control access to the Web and cloud applications based on risk, including contextual factors like time of day, user, device security posture, geolocation, network connection, etc.
- Enforce consistent policies for all user access - in the office, on the road, and at home - by applying Zero Trust Network Access principles.
- Optionally, block malware (including zero-day threats) from reaching endpoints and networks by rendering websites in isolated containers located on remote servers far from the endpoint.
- App Connectors allow seamless connectivity to public/private clouds and data centers, ensuring an end-to-end Zero Trust secure connection from device to application.

Enforcing dynamic policies at the endpoint
Mobile-friendly
- Dynamic ZTNA policies are enforced as closely as possible to the end user, meaning at the endpoint. This eliminates chokepoints as well as protects device data and meets the most advanced NIST SP 800-207 Zero Trust Architecture recommendations.
- On-premises to cloud doesn’t happen overnight. Neither does full Zero Trust. Absolute is the only vendor to provide a world-class VPN and ZTNA solution as part of its platform, allowing for rapid or gradual ZTNA adoption.

Get maximum value out of your security spend
Mitigate risk and strengthen your compliance posture with Absolute
- Assure security efficacy via self-healing
- Streamlined collection of compliance evidence
- Critical application availability and uptime for incident response
- Reduced mean time to response
- Ease of enforcement of security configurations at scale
- Improved risk score
Enable the secure device lifecycle
Reduce complexities across endpoints, applications, and network access that are causing inefficiencies and risk exposure.
- High visibility from the endpoint
- Reduced number of helpdesk tickets
- Reduced number of rogue devices and apps
- Improved business-specific KPIs
- Vendor consolidation
- Real-time telemetry from devices & network
Maximize your workforce’s productivity - wherever they do their work
Don't let security be a barrier to an optimized employee experience.
- Provide always-on, work-from-anywhere capabilities for your workforce
- Optimized user experience and uptime
- Reduced management infrastructure
- Resilient, reliable network apps
- User adoption of key applications
- Guaranteed, continuous service delivery
Get maximum value out of your security spend


Expect
Innovation.
Join us for three days of deep-divetechnical sessions, high-levelnetworking, and exclusive first-looks atnew resiliency tech.
Explore our products

Serves as your source of truth for device and application health.

Provides you a lifeline to protect at-risk devices and data.

Delivers application self-healing and confident risk response.

Provides seamless and proactive patch management.

Offers remediation of security vulnerabilities through automated workflows.

Boosts ransomware preparedness and time-to-recovery.

Watch in real-time as Absolute'sself-healing technologyautomatically repairscompromised controls withouthuman intervention.

Engage with peers and Absoluteexperts to discuss the practicalapplication of the Zero Trustframework and endpoint hygiene.

Join high-level social eventsdesigned to foster collaborationbetween the industry's brightestsecurity minds and CISOs.
Related Product Packages
Specifically tailored capabilities for Chromebook users.
Specifically tailored capabilities for Windows student devices.
Specifically tailored capabilities for Education customers.
Featured resources
Secure Access FAQ
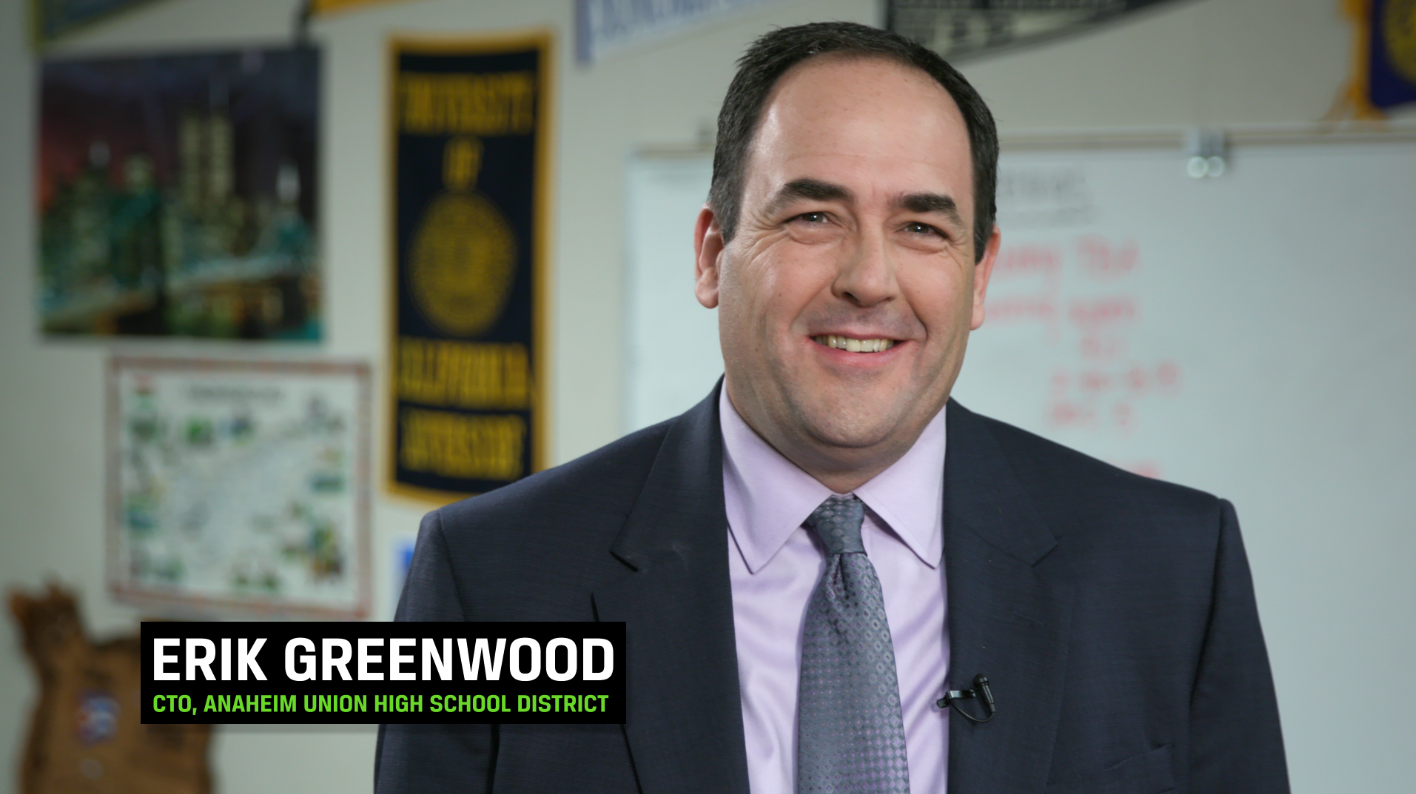
Absolute Secure Access is one of the company’s core product lines, which was added through the acquisition of NetMotion in July 2021. The product portfolio provides resilient network connectivity for users to securely access critical resources in the public cloud, private data centers, and on-premises. These products allow users to transition from an optimized, secure tunnel to a resilient Zero Trust approach, without impairing productivity or admin controls.
Absolute Secure Access encompasses these products:
- Absolute Core provides security and confidentiality for data in motion by means of encryption and access controls. It also offers benefits to the end user, such as making tunnel and network sessions resilient and optimizing streaming video and audio.
- Absolute Edge provides a software-defined perimeter via Zero Trust Network Access, creating a context-based, logical access boundary around an application or set of applications – wherever they're hosted. It shields applications from the Internet, making them invisible to unauthorized users. Access policies are enforced at the endpoint, avoiding latency and any data transgression.
- Absolute Enterprise is a converged, resilient cloud-native SSE platform that includes Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), Private Access (ZTNA), Data Loss Prevention (DLP) and Remote Browser Isolation (RBI) into a single platform. It also includes proactive anomaly detection (AI Threat Insights) and over 70+ dashboards of user, device, network, and application behavior (Insights for Network) as well as Endpoint Compliance that gives administrators additional visibility, control, and resilience over user devices.
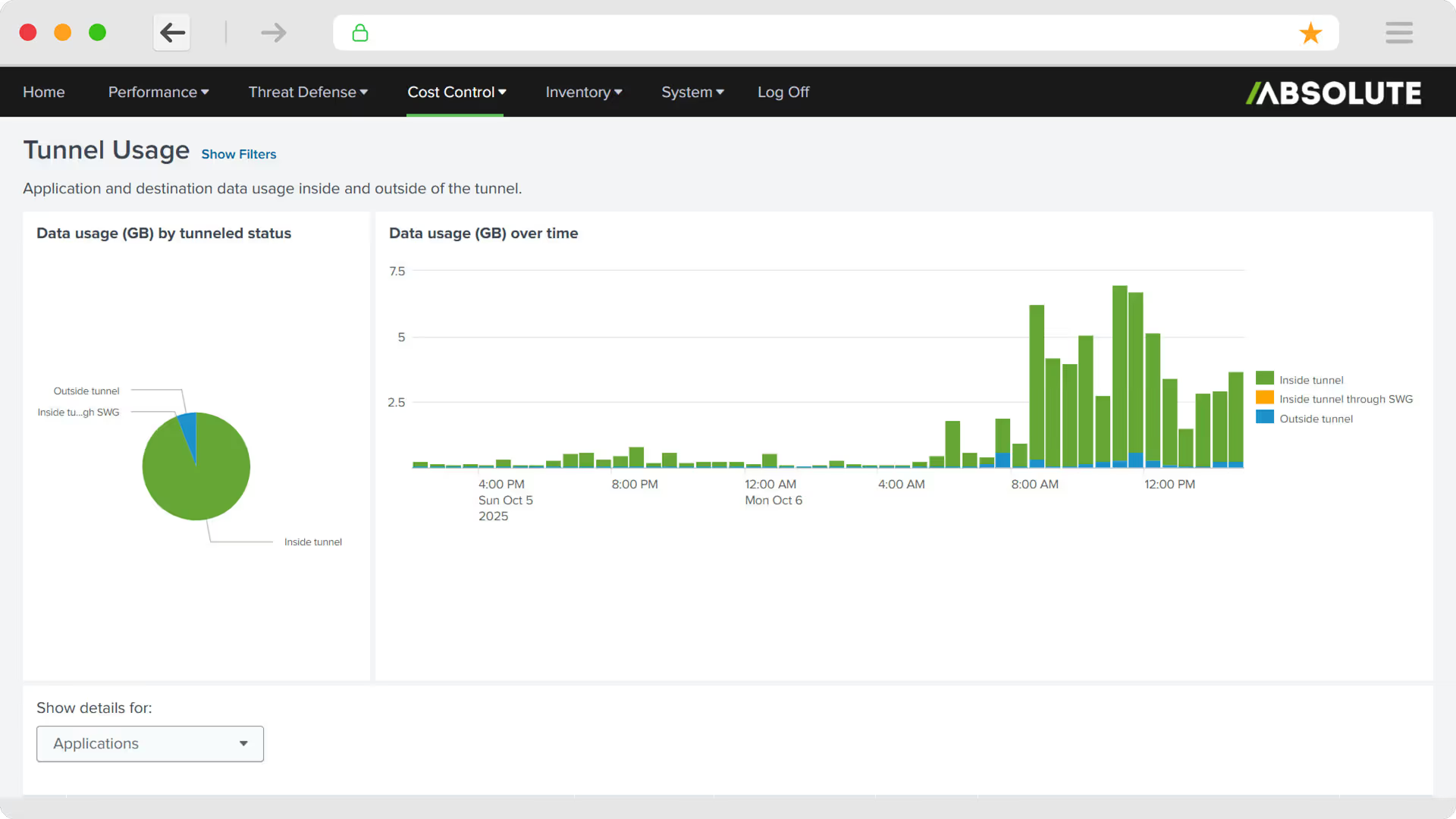
- Absolute Insights for Network™ offers diagnostic and experience monitoring capabilities across endpoints and network, allowing organizations to proactively monitor, investigate, and remediate end user performance issues quickly and at scale, even on networks that are not company-owned or managed.
Absolute Secure Access packages are offered in three flavors: Absolute Core™, Absolute Edge ™, and Absolute Enterprise with the included products and capabilities as outlined below. Regional variations might be available.
- Absolute Core
- Secure, optimized tunnel
- ZTNA dynamic policy enforcement
- Network Access Control (NAC)
- Absolute Edge
- Includes Absolute Core, and adds:
- AI-powered web protection (“Shadow IT”)
- Absolute Insights for Network (70+ dashboards)
- AI Threat Insights
- Absolute Enterprise
- Includes Absolute Edge, and adds:
- Multiple AV scans
- Data Loss Prevention (DLP)
- Remote Browser Isolation (RBI)
- Content Disarm and Reconstruction (CDR)
- Endpoint Compliance
For Absolute Edge customers, Absolute offers the Absolute Secure Web Gateway Service (powered by Ericom) add-on module that tightly integrates with the extensive policy capabilities in Absolute Secure Access. It strengthens an organization’s security posture while improving end user experience.
Customers can easily upgrade their subscription between Absolute Core, Absolute Edge, and Absolute Enterprise. Capabilities are additive and enabled via a software license key.
Absolute Enterprise converges Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), Private Access (ZTNA), Data Loss Prevention (DLP) and Remote Browser Isolation (RBI) into a single platform. Absolute Enterprise provides real-time data and threat protection against advanced zero-day and cloud-enabled threats and offers Endpoint Compliance that enables additional visibility, control, and resilience on devices.
Absolute Secure Access supports Apple® iPad and iPhone devices (iOS 11 and later), Apple MacOS (10.13 and later), Android devices (running on Android 5.0 or later), Android for Work, Samsung KNOX, Windows Pro Tablets, laptops, and other devices running Windows 8, 10, and 11.