Give your IT team constant visibility into endpoints
The work-from-anywhere era has given newfound significance to endpoint visibility. Inconsistent visibility affects your IT team’s ability to support and resolve user issues. Most cyberattacks begin on endpoints, not firewalls or servers, which makes endpoint visibility even more essential.
Highlights

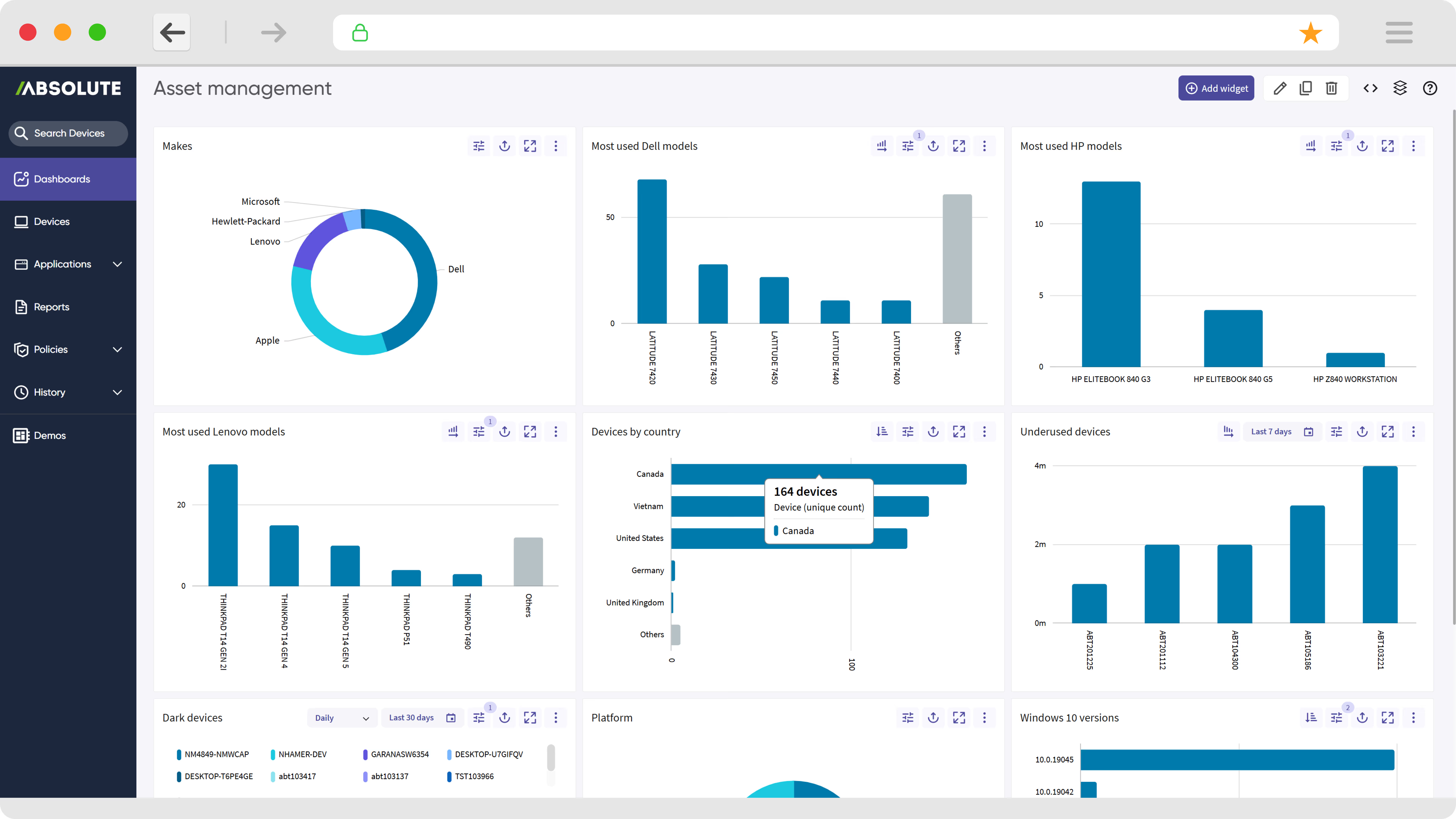
Report and alert on hundreds of hardware attributes, leverage pre-built and custom reports, track new device activations and connection history, and track the evolution of offline devices.

Assess installed software on your devices to identify vulnerable apps or versions, policy non-compliance, shadow IT, and possible license non- compliance.

Determine your ROI for online tools and subscriptions by comparing usage patterns across your teams. Identify if devices are accessing unsecure or inappropriate websites or applications.

Report on encryption and anti-virus/malware status across your device population, monitor evolution of encryption status over time.

Assess average daily device usage across different device groups to detect under-utilized devices or anomalous usage.

Discover sensitive data (e.g., PII, PHI, company IP) across your device fleet and identify devices that are syncing sensitive files with cloud storage services.

See all your enrolled devices, on and off your corporate network.

Configure custom visualizations to track current compliance status and historical trends related to devices and applications.

Obtain tailored endpoint, security and compliance information across your environment by asking questions to the Absolute AI Assistant.
Get the truth from your devices, apps, and data
Discover savings within your budget
- Trust that you’re not missing anything — thanks to an always-on connection that is provided by Absolute Persistence® technology.
- Embedded in the firmware of more than 600 million endpoints, Absolute will automatically reinstall itself to remain healthy even if tampered with. This enables consistent visibility.
- Inventory your hardware and software assets automatically — then generate reports on hardware status, software, OS, geolocation, and hundreds of other data points that Absolute collects for you.
- Maximize the return on your tech investments with reports on device and software usage. Identify underused devices to repurpose across your teams.
- Detailed Web usage and ROI analytics demonstrate how users are leveraging Web tools to help you measure value.

Know where your devices are – at any given time
Guarantee uninterrupted visibility
- Track device location with a full 365 days of history, helping you to locate lost or stolen endpoints. Count on real-time device and location updates - even during an emergency.

Stay ahead of cybersecurity threats and vulnerabilities
Gain insight into your risk exposure
- Identify threats before they become incidents. Keep your employees, customers, and auditors happy with customized status reports on endpoint encryption, anti-malware, and other mission critical applications.
- Identify access to inappropriate or unsecure content that may pose risks, compare usage patterns, and detect use of unapproved Web apps.
- Scan your endpoints for sensitive data like financial information, social security numbers, or intellectual property. Know when it’s on an unsecured device, even off-network.

Obtain device and security insights
Build custom dashboards for your unique requirements
- Configure widgets, dashboards and reports aligned with IT and security policies.
- Analyze current status and historical trends across attributes, including asset management, device risk, compliance, and app usage.
- Access granular insights on encryption status, device location, and web or software activity.
- Query for tailored device and security information across your environment using the Absolute AI Assistant.

What our customers love about Absolute Visibility

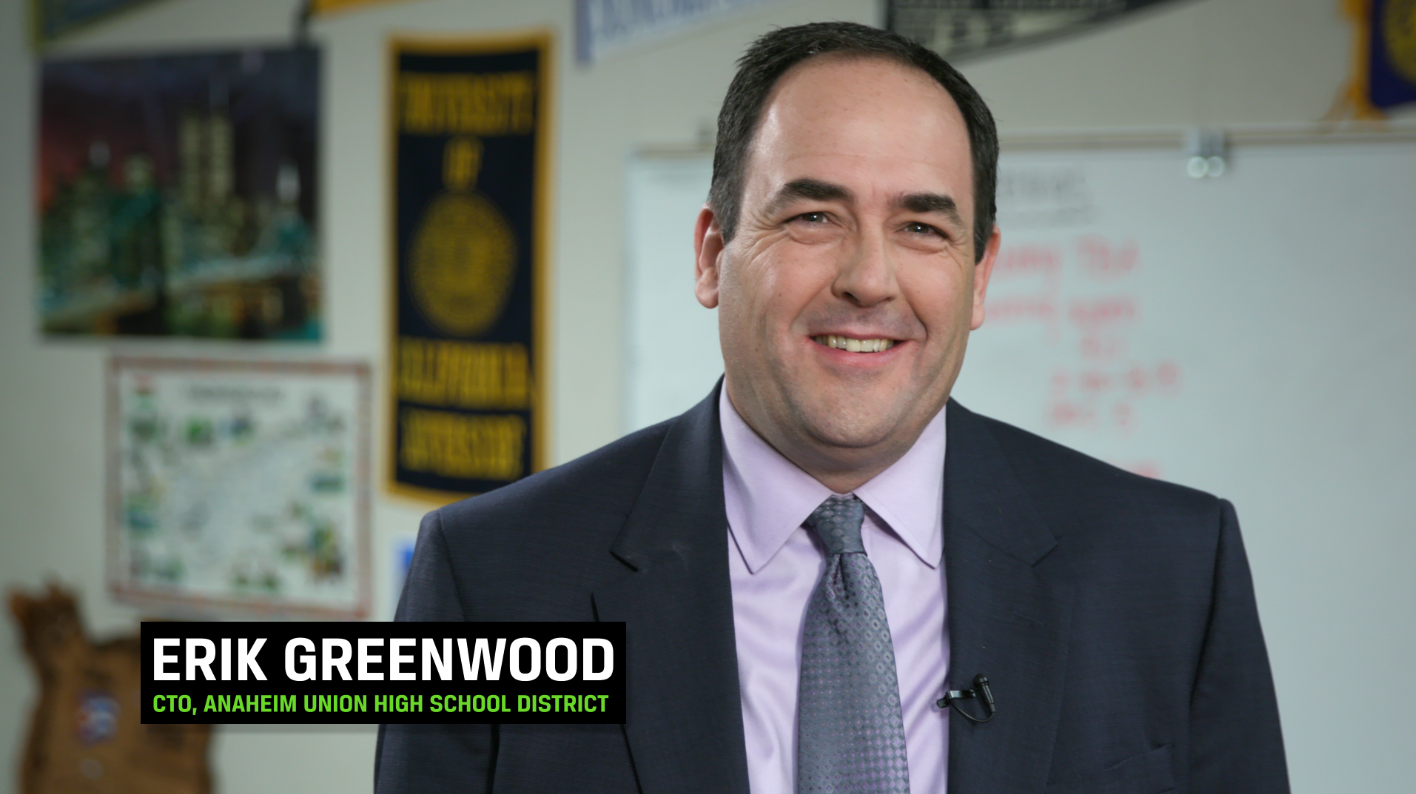
Absolute and their Student Technology Analytics give us the ability to see how and when our devices are being used and correlate that information to student outcomes.
Simple and flexible packages
Discover how Absolute keeps your devices secure, resilient, and always connected.
Explore Secure Endpoint products

Serves as your source of truth for device and application health.

Provides you a lifeline to protect at-risk devices and data.

Delivers application self-healing and confident risk response.

Provides seamless and proactive patch management.

Offers remediation of security vulnerabilities through automated workflows.

Boosts ransomware preparedness and time-to-recovery.
Explore Secure Access Products

Built from ground up for mobility and the modern edge.

Delivers the best user experience for the software-defined perimeter.

Comprehensive SSE provides security controls and threat protection across web, cloud, and private apps.

Boosts diagnostics and remediation for digital experience monitoring.

Web security that protects data, prevents threats, and secures access to cloud apps.
Related product packages
Specifically tailored capabilities for Chromebook users.
Specifically tailored capabilities for Windows student devices.
Specifically tailored capabilities for Education customers.
Featured resources
Device recovery FAQ
Absolute Secure Endpoint is one of our company’s core product lines, which leverages the unbreakable connection provided by Absolute Persistence® to enable IT and security personnel to monitor and address computers' problems and enables the computers and their mission-critical applications to self-heal. This helps with IT management, strengthening a company’s security posture, and maintaining compliance.
The Absolute Secure Endpoint product portfolio contains a variety of product packages:
- Absolute Visibility
- Absolute Control
- Absolute Resilience
- Absolute Resilience for Security
- Absolute Resilience for Automation
- Absolute Ransomware Response
Other variants, such as Absolute Resilience for Student Devices, may be offered to meet particular use cases or geographic market needs.
Absolute Visibility is the entry service tier in the Absolute Secure Endpoint portfolio. Absolute Visibility collects data about the endpoints' location, security posture, and hardware/software inventory. It provides analysis of software, Web applications, and hardware utilization as well as identifies potential failure points, sensitive data, and suspicious use patterns.
Absolute Control is the mid-service tier in the Absolute Secure Endpoint portfolio. Absolute Control adds to Absolute Visibility’s capabilities to control endpoints over the Internet, allowing for critical functions such as remote file deletion and data wipe, freezing devices on demand when at-risk, end user messaging, as well as establishing geo-fences and alerts.
Absolute Resilience is the third product edition in the Absolute Secure Endpoint product portfolio. Compared to Absolute Control, it adds further capabilities to secure endpoints from IT or security risks, respond to unexpected downtime due to security breaches and incidents, and enable Application Resilience to automatically monitor and detect unhealthy applications and automatically heal them.
Absolute Ransomware Response is a stand-alone offering, which provides capabilities and services to assess an organization's ransomware preparedness and cyber hygiene across endpoints; ensures mission-critical security applications such as anti-malware and device management tools remain healthy and capable of self-healing; and expedites the quarantine and recovery of endpoints if a ransomware attack occurs.
Customers can easily upgrade/downgrade their product subscriptions between Absolute Visibility, Control, Resilience, Resilience for Security and Resilience for Automation. Capabilities are additive and enabled via a software license key.
Absolute Ransomware Response is offered as a stand-alone solution primarily for security-conscious customers. Add-on options are offered for Absolute Control, Resilience, Resilience for Security and Resilience for Automation customers.
Absolute can be purchased through leading device manufacturers, resellers, and distributors. Contact us and we would be happy to help you with this process.