Automated Recovery, Intelligent Compliance and Resilient Endpoint Operations
Maintaining compliance and restoring devices at scale
In today’s distributed, hybrid first world, endpoint environments are more complex, more fragile, and more frequently targeted than ever before. IT and Security teams must maintain device health, ensure compliance, respond to incidents at scale, and keep employees productive while managing shrinking resources and growing risk.
With the launch of Absolute Secure Endpoint 11, we are doubling down on our commitment to build the most resilient and intelligent endpoint platform on the market, enabling enterprise organizations to stop downtime at scale. This release delivers major advancements in automated recovery, intelligent compliance monitoring, data driven insights and ecosystem interoperability to help enterprises prevent disruption and recover faster.
Secure Endpoint 11 includes three key releases (11.0.0, 11.0.1 and 11.0.2), culminating in a set of high impact enhancements that support our Cyber Resilience platform pillars of:
- Unbreakable Visibility and Control
- Protection and Remediation
- Rapid Operational Recovery
What’s New in Secure Endpoint 11
1. Rehydrate Failsafe: Automated Endpoint Recovery for Unattended Devices
Endpoint downtime caused by ransomware, a corrupted operating system, or critical system failures has traditionally required shipping devices, USB restoration workflows, or manual end-user engagement. With Rehydrate Failsafe, Absolute eliminates those dependencies.
Failsafe automatically triggers a pre‑configured Rehydrate recovery playbook with no user interaction required. Devices can automatically recover to a trusted, compliant, ready-to-work state, even when they are remote, in transit, or unattended.
Key benefits:
- Restore remote devices after cyber incidents with zero user action
- Automate recovery at scale across hundreds or thousands of endpoints
- Reduce IT fieldwork, helpdesk tickets, and time to remediation
- Ensure devices return to a secure, compliant baseline image
Rehydrate remains the only enterprise recovery technology capable of executing playbooks directly from firmware, bypassing the OS entirely, even when it is damaged or tampered with.

2. Rehydrate Playbook Enhancements: Restoration Using Local Recovery Images
Enterprises can now restore devices using a locally hosted recovery image stored on a dedicated disk partition. This eliminates reliance on external network access, reduces bandwidth consumption, and accelerates large-scale restorations during widespread incidents, helping organizations recover faster with less strain.
Organizations with globally distributed or bandwidth constrained environments (such as retail, oil & gas, or field services) can now deploy certified “golden images” more efficiently and reliably.

3. Device Compliance Policies: Simplifying Compliance Drift Management
As organizations scale, endpoint compliance naturally degrades over time: encryption is disabled, AV stops running, unauthorized apps appear, OS versions go out of date, devices leave geofenced regions, or simply stop reporting in.
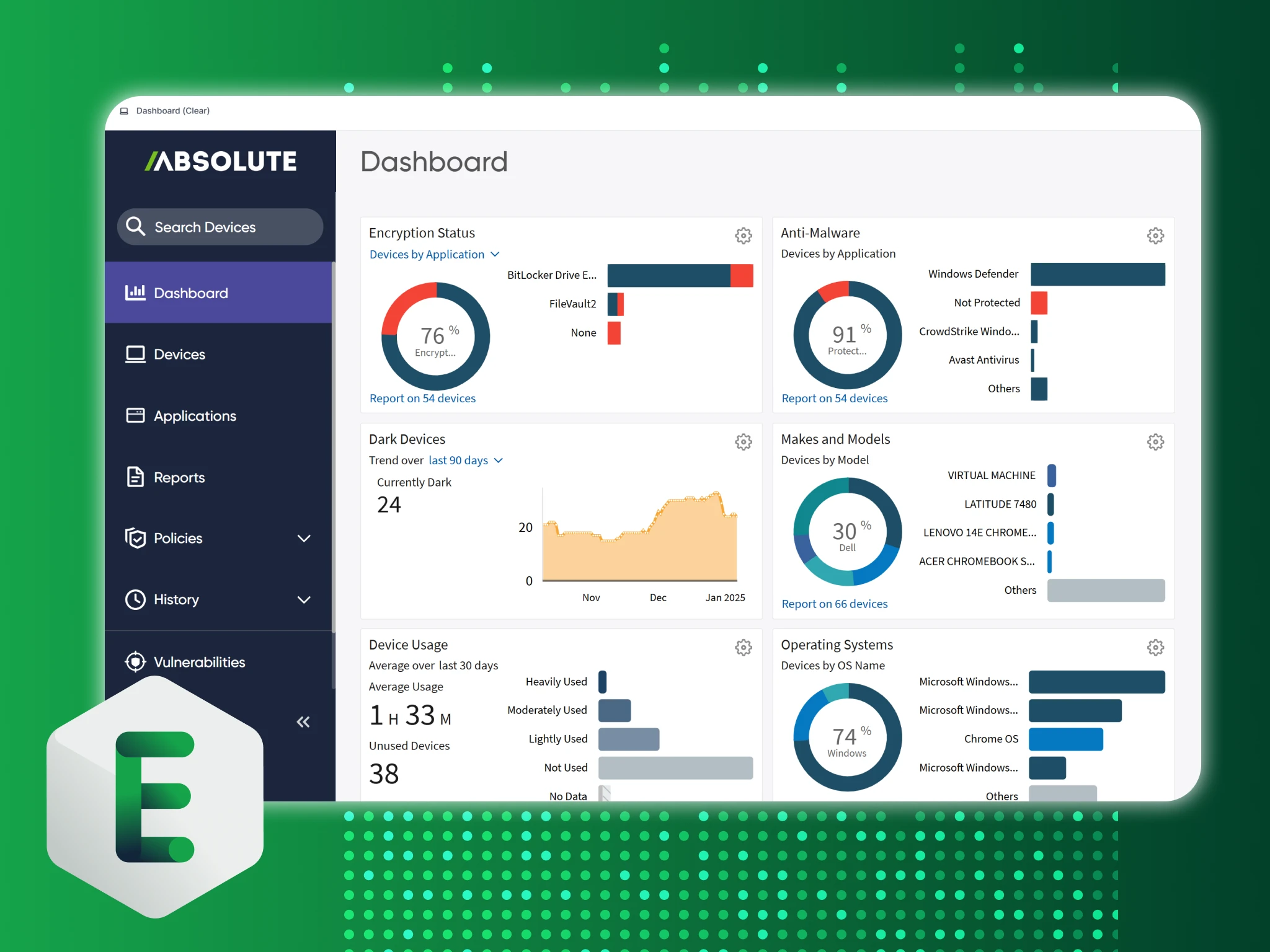
To address these challenges, Secure Endpoint 11 introduces Device Compliance Policies, giving IT and Security teams a unified and automated way to assess compliance based on attributes like:
- Encryption status
- Antivirus health
- OS version
- Device Location
- Health of security or business applications through the Application Resilience or Required Applications policies
Out of compliance devices can be quickly identified, flagged, and remediated using automated enforcement and integrated workflows.
This capability also sets the stage for integration with Absolute Secure Access through the upcoming Comply-to-Connect (C2C) solution, allowing device compliance posture to directly inform access decisions and strengthening our consolidated platform story.

4. AI Assistant Enhancements: Smarter, Faster Endpoint Intelligence
Building on the AI-powered experience introduced last year, Secure Endpoint 11 expands the capabilities of the Absolute AI Assistant with:
- More accurate responses based on customer usage patterns
- Export capabilities for audit or collaboration requirements
Customers can ask natural language questions and instantly receive actionable, visual insights across their device fleets. Example prompts could include “Which devices haven’t called in over 90 days?” or “Show encryption status by country”.
The AI Assistant is deeply integrated with Customizable Dashboards to support faster discovery, analysis, and decision making.
5. Public API Expansion: Deeper Ecosystem Interoperability
To help customers integrate Absolute Secure Endpoint into their broader IT and security workflows, Secure Endpoint 11 significantly expands Public API coverage to support:
- Custom Data Collector datapoints
- Endpoint Data Discovery actions
- User Management operations
This enables organizations to orchestrate Absolute Secure Endpoint telemetry and actions within SIEM, SOAR, ITSM and customer enterprise systems, supporting automated enforcement, remediation and reporting across the ecosystem.
Why Secure Endpoint 11 Matters
Secure Endpoint 11 directly addresses the challenges modern IT and security teams face:
- Minimize downtime during incidents: Automated recovery reduces recovery time from days or weeks to hours without requiring physical access or user intervention.
- Improve compliance and reduce risk: New compliance policy capabilities help organizations maintain alignment with internal standards and external frameworks like CIS, NIST, GDPR, and HIPAA.
- Enhance visibility and decision-making: Expanded dashboards and AI Assistant enhancements surface insights faster and more intuitively.
- Scale operations without scaling effort: Automation features and API expansions reduce manual work, lower operational overhead, and improve IT efficiency.
- Strengthen device and data protection: Rehydrate’s firmware-level execution ensures devices remain recoverable even when the operating system is compromised, a capability unmatched by any other endpoint platform.
Looking Ahead
Secure Endpoint 11 represents a major advancement in our mission to help organizations build resilient, self healing endpoint environments. With automated recovery, intelligent compliance, richer data insights, and expanded interoperability, our customers can better withstand disruptions, reduce risk, prevent operational disruption and keep their workforces productive.
To learn more, check out the following resources:
- Rehydrate datasheet
- Rehydrate interactive demo
- Device Compliance Policies datasheet
- AI Assistant interactive demo