Shrink Your Endpoint Attack Surface Fast

The problem
Scanning for vulnerabilities isn’t the same as fixing them. Security teams are drowning in alerts, juggling misconfigurations, delayed patches, and failed controls. Ad-hoc changes go untracked. Agents fail. Critical settings change. The longer a vulnerability sits exposed, the wider your attack surface becomes.
Noise hides the threats that matter
Alert fatigue slows remediation. Mean time to fix stretches into weeks. Exploits don’t wait for your next review cycle, they capitalize on misconfigurations, disabled controls, and unpatched systems the moment they appear.
Every time we add another tool, we add complexity. And complexity is one of our biggest vulnerabilities. We’re realists, we know bad things can happen, and we’re here to make sure you can recover.
Stop assuming. Start enforcing.
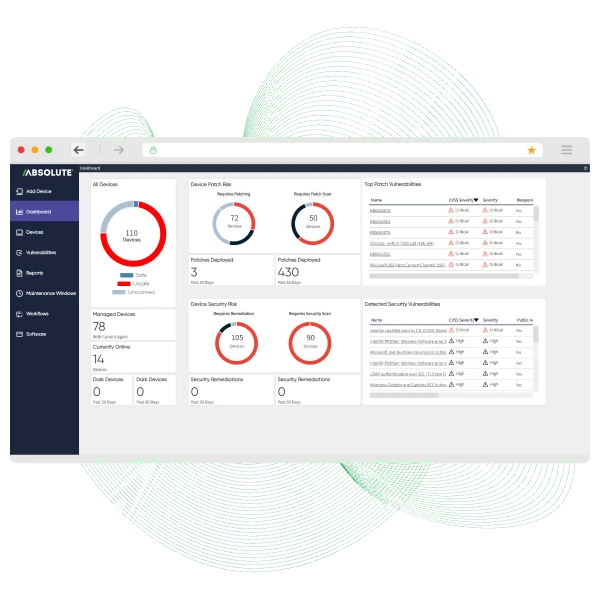
Absolute Security’s firmware-anchored connection gives you an unbreakable line of control to every endpoint, on or off the network. With Absolute Resilience for Automation, you can continuously discover and prioritize configuration vulnerabilities that matter. Policy-driven automation corrects them instantly, shrinking exploitable windows from days to minutes. This eliminates the guesswork, freeing your team from alert fatigue to focus on what matters. This isn't about finding problems; it's about making them go away.
See certainty in action: security, enforced.
Tired of guessing? Stop reacting and start enforcing. See how our undeletable connection gives you absolute control over your endpoint security posture.
- Prioritize real threats: Focus on vulnerabilities attackers are actively exploiting.
- Automate remediation: Apply configuration and patch fixes instantly at scale.
- Verify enforcement: Confirm endpoints return to a secure, compliant state.



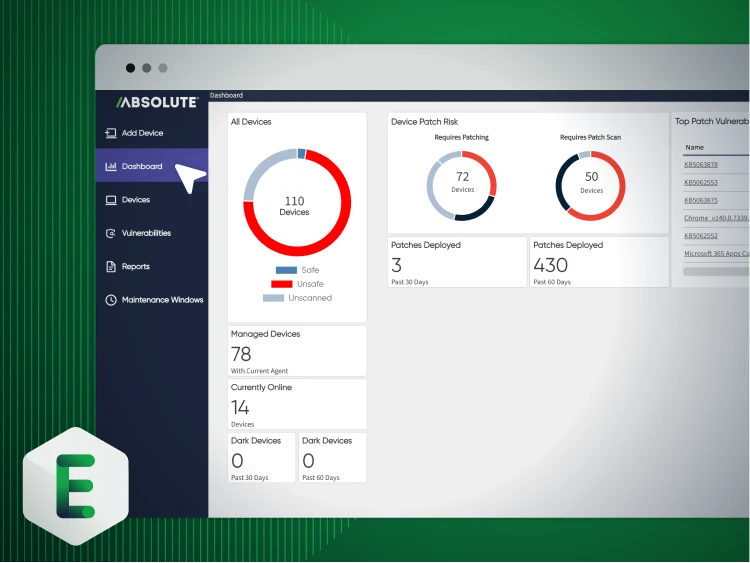
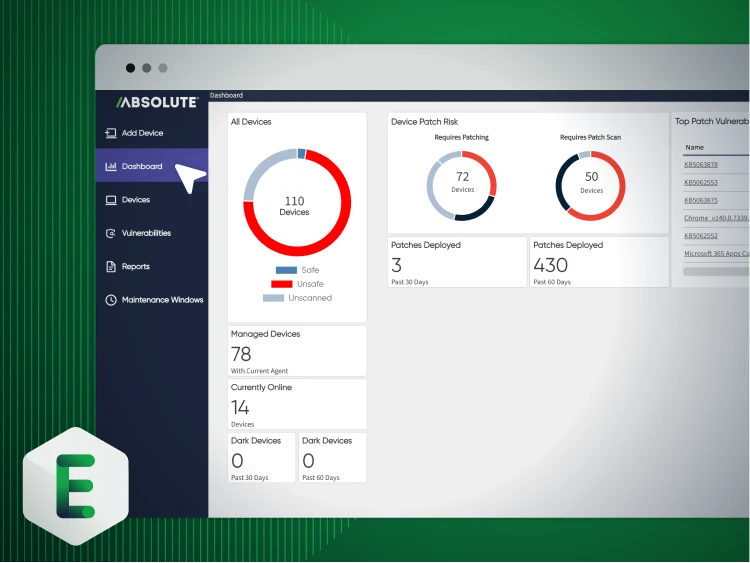
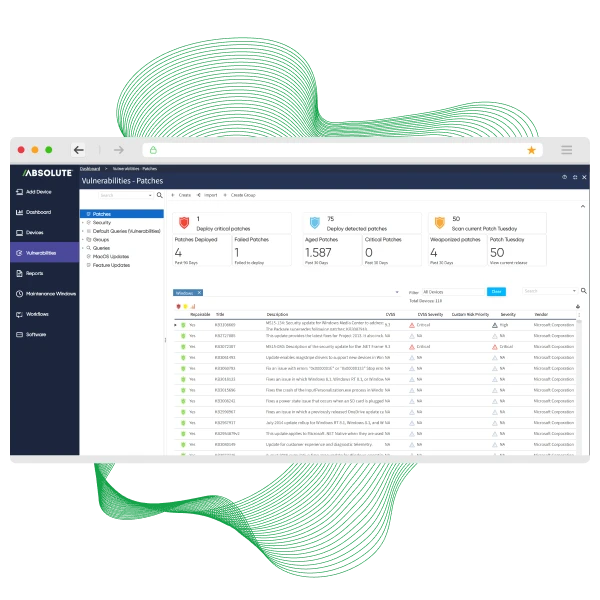
EECO fixes vulnerabilities at scale
EECO, a leading electrical distributor with 300+ employees across 12 locations, needed to remediate a growing backlog of critical misconfigurations and vulnerabilities across its distributed workforce. Years of inconsistent MSP performance left them without unified visibility or a reliable way to enforce configuration standards. Learn how EECO:
- Automated patching and configuration remediation at scale using pre‑built vulnerability scripts — dramatically reducing time and operational cost.
- Verified remediations with built‑in vulnerability scanning and real‑time device reporting to ensure issues were actually fixed.
- Centralized endpoint and configuration management after bringing operations back in‑house for improved visibility and tighter security control.
Essential capabilities for configuration vulnerability management
Identify misconfigurations, disclosed vulnerabilities, and policy drift across endpoints.
Focus remediation on vulnerabilities that materially expand your attack surface.
Automatically correct configuration gaps and enforce approved baselines.
Deliver and execute remediation commands—even off-network.
Confirm endpoints return to a compliant, hardened state.
Generate exportable proof of remediation and compliance posture.
Elevate your IT strategy with intelligent automation
Automation isn’t about replacing people—it’s about freeing teams from repetitive tasks that stifle strategic thinking. When skilled professionals are buried in alerts and manual scripts, their true value goes untapped.
- Discover how to shift your team from reactive problem-solvers to proactive architects.
- Learn why endpoint management automation is the key to elevating your IT function.

Dive into vulnerability remediation
Every unresolved vulnerability is an open door. In a tailored Secure Endpoint demo, see how policy-driven automation discovers, prioritizes, and remediates vulnerabilities before attackers exploit them.
- Prioritize real risk: Focus on vulnerabilities that actively expand your attack surface.
- Enforce baseline security: Automatically correct misconfigurations at scale.
- Prove remediation: Deliver verified, audit-ready evidence of enforcement.
Featured resources for vulnerability management
Configuration vulnerability management FAQ
It’s an insecure setting or misconfiguration in your software, network devices, or operating systems that an attacker can exploit. Unlike a software flaw (like a CVE), this vulnerability isn't a bug in the code itself. Instead, it’s a weakness created by how the system is set up—think an open admin port, unnecessary user permissions, or disabled security features.
They’re essentially two sides of the same coin, but they address different problems. Traditional vulnerability management focuses on patching software flaws (CVEs) to fix bugs in the code. Configuration vulnerability management focuses on correcting insecure settings and policy drift within the system itself. You can be fully patched and still be vulnerable because a port was left open or a security control was disabled.
Yes, most scanners can detect misconfigurations. The real question is, what happens next? Most tools just add it to a report, creating more noise for your team to sift through. The challenge isn't just finding the problem; it's fixing it with certainty and at scale, without burying your team in false positives or low-impact alerts.
This is a fair question. The key is moving from blunt, all-or-nothing actions to policy-driven enforcement. You define the "golden state" for your configurations. The platform then only corrects deviations from that specific baseline. It’s not a blind action; it’s a precise, automated correction that brings an endpoint back into compliance, often without any user impact.
This is where the old model truly breaks down. Waiting for a device to connect to the VPN to receive a configuration update is a losing game. A persistent, firmware-level connection is essential. It ensures that your enforcement policies reach every device, regardless of its network status or location, allowing you to correct configuration drift the moment it happens, not days or weeks later.
