Shrink Your Endpoint Attack Surface Fast

The problem
Scanning for vulnerabilities isn’t the same as fixing them. Security teams are drowning in alerts, juggling misconfigurations, delayed patches, and failed controls. Ad-hoc changes go untracked. Agents fail. Critical settings change. The longer a vulnerability sits exposed, the wider your attack surface becomes.
Noise hides the threats that matter
Alert fatigue slows remediation. Mean time to fix stretches into weeks. Exploits don’t wait for your next review cycle, they capitalize on misconfigurations, disabled controls, and unpatched systems the moment they appear.
Every time we add another tool, we add complexity. And complexity is one of our biggest vulnerabilities. We’re realists, we know bad things can happen, and we’re here to make sure you can recover.
Stop assuming. Start enforcing.
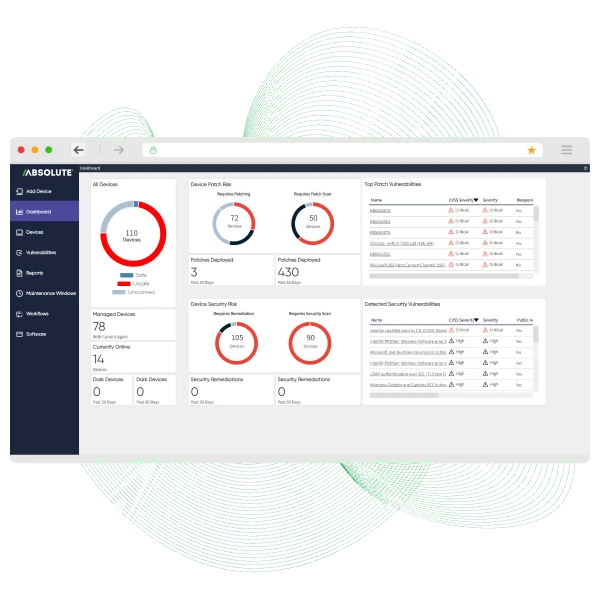
Absolute Security’s firmware-anchored connection gives you an unbreakable line of control to every endpoint, on or off the network. With Absolute Resilience for Automation, you can continuously discover and prioritize configuration vulnerabilities that matter. Policy-driven automation corrects them instantly, shrinking exploitable windows from days to minutes. This eliminates the guesswork, freeing your team from alert fatigue to focus on what matters. This isn't about finding problems; it's about making them go away.
See certainty in action: security, enforced.
Tired of guessing? Stop reacting and start enforcing. See how our undeletable connection gives you absolute control over your endpoint security posture.
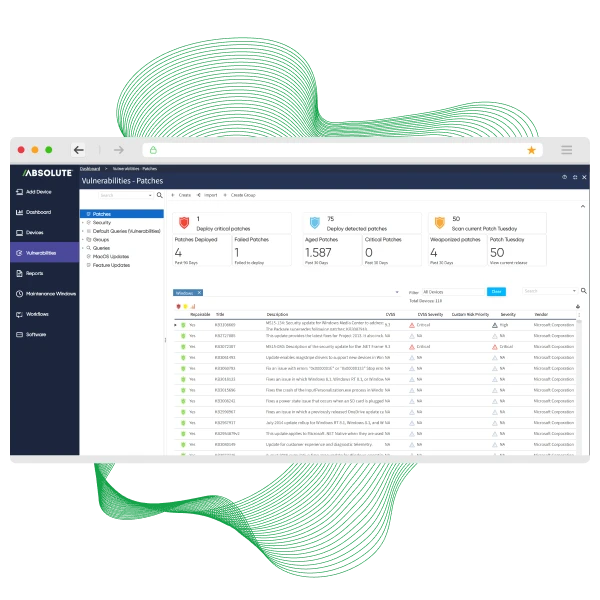
- Prioritize real threats: Focus on vulnerabilities attackers are actively exploiting.
- Automate remediation: Apply configuration and patch fixes instantly at scale.
- Verify enforcement: Confirm endpoints return to a secure, compliant state.



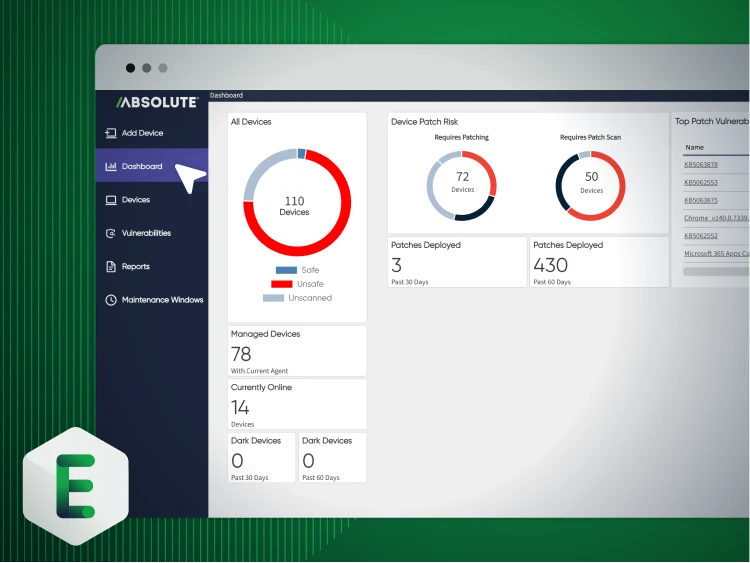
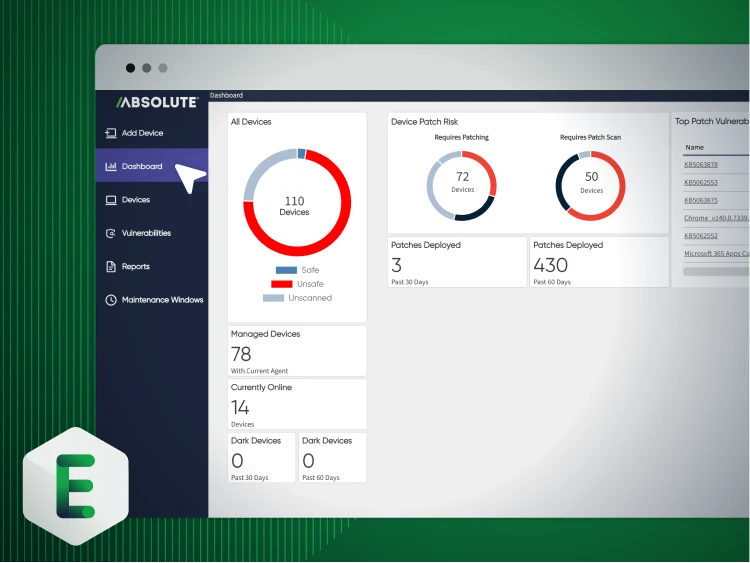
EECO fixes vulnerabilities at scale
EECO, a leading electrical distributor with 300+ employees across 12 locations, needed to remediate a growing backlog of critical misconfigurations and vulnerabilities across its distributed workforce. Years of inconsistent MSP performance left them without unified visibility or a reliable way to enforce configuration standards. Learn how EECO:
- Automated patching and configuration remediation at scale using pre‑built vulnerability scripts — dramatically reducing time and operational cost.
- Verified remediations with built‑in vulnerability scanning and real‑time device reporting to ensure issues were actually fixed.
- Centralized endpoint and configuration management after bringing operations back in‑house for improved visibility and tighter security control.
Essential capabilities for configuration vulnerability management
Elevate your IT strategy with intelligent automation
Automation isn’t about replacing people—it’s about freeing teams from repetitive tasks that stifle strategic thinking. When skilled professionals are buried in alerts and manual scripts, their true value goes untapped.
- Discover how to shift your team from reactive problem-solvers to proactive architects.
- Learn why endpoint management automation is the key to elevating your IT function.

Dive into vulnerability remediation
Every unresolved vulnerability is an open door. In a tailored Secure Endpoint demo, see how policy-driven automation discovers, prioritizes, and remediates vulnerabilities before attackers exploit them.
- Prioritize real risk: Focus on vulnerabilities that actively expand your attack surface.
- Enforce baseline security: Automatically correct misconfigurations at scale.
- Prove remediation: Deliver verified, audit-ready evidence of enforcement.
Featured resources for vulnerability management
Configuration vulnerability management FAQ
Es una configuración insegura o una mala configuración en su software, dispositivos de red o sistemas operativos que un atacante puede explotar. A diferencia de una falla de software (como un CVE), esta vulnerabilidad no es un error en el código en sí. En cambio, es una debilidad creada por cómo está configurado el sistema: piense en un puerto de administrador abierto, permisos de usuario innecesarios o funciones de seguridad deshabilitadas.
Esencialmente son dos caras de la misma moneda, pero abordan problemas distintos. La gestión tradicional de vulnerabilidades se enfoca en parchear fallas de software (CVE) para corregir errores en el código. La gestión de vulnerabilidades de configuración se enfoca en corregir configuraciones inseguras y la deriva de políticas dentro del propio sistema. Puede estar completamente parchado y seguir siendo vulnerable porque se dejó un puerto abierto o se deshabilitó un control de seguridad.
Sí, la mayoría de los escáneres puede detectar malas configuraciones. La verdadera pregunta es: ¿qué pasa después? La mayoría de las herramientas solo lo agrega a un informe, creando más ruido para que su equipo lo revise. El desafío no es solo encontrar el problema, sino corregirlo con certeza y a escala, sin sepultar a su equipo en falsos positivos o alertas de bajo impacto.
Es una pregunta válida. La clave está en pasar de acciones toscas de todo o nada a una aplicación guiada por políticas. Usted define el "estado dorado" para sus configuraciones. Luego, la plataforma solo corrige las desviaciones respecto de esa línea base específica. No es una acción a ciegas; es una corrección automatizada y precisa que devuelve un endpoint al cumplimiento, a menudo sin impacto alguno para el usuario.
Aquí es donde el modelo antiguo realmente se desmorona. Esperar a que un dispositivo se conecte a la VPN para recibir una actualización de configuración es una batalla perdida. Una conexión persistente a nivel de firmware es esencial. Garantiza que sus políticas de aplicación lleguen a cada dispositivo, independientemente de su estado de red o ubicación, permitiéndole corregir la deriva de configuración en el momento en que ocurre, no días o semanas después.
