Cybersecurity That Stays On — Even Under Attack
Self-healing endpoint security starts here
Cyber resilience that keeps your business running, no matter what
Powered by Absolute Persistence®, our patented, firmware-embedded technology establishes an unbreakable, always-on connection to every endpoint in your fleet. This is true endpoint resilience. Your organization maintains visibility, control, and operational uptime even when devices are re-imaged, compromised, or fall out of compliance.
Critical data, business applications, and productivity remain protected, no matter how persistent the threat is.

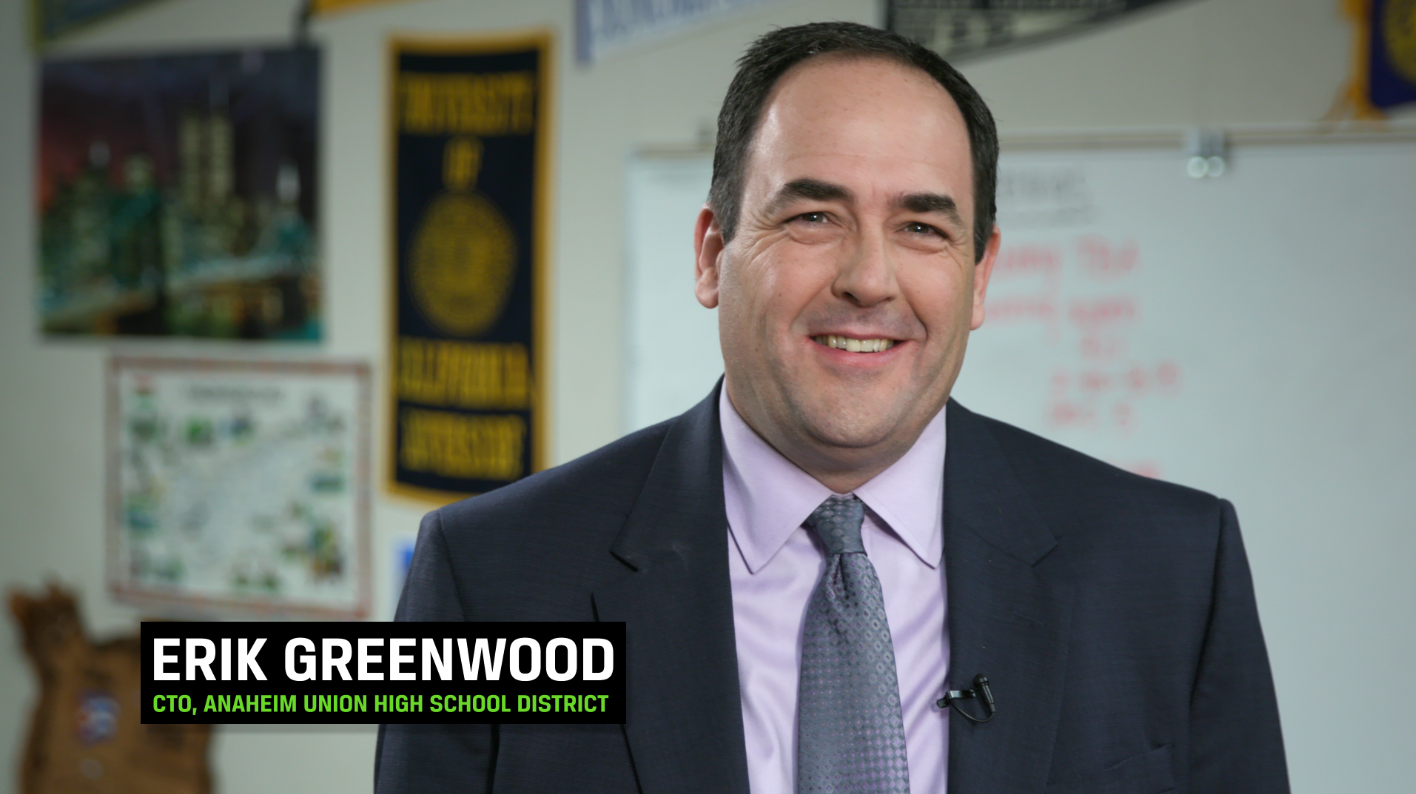
Absolute Secure Endpoint is a very simple, cost-effective solution to track hardware assets. It makes IT people’s lives easier – and that’s good, because we have enough to worry about. We are amazed by the Absolute Persistence® technology. An IT team member took a hard drive out and put it on another machine. The Absolute software agent created itself on the new machine and the old machine with a new hard drive. Indestructible.
Recover faster. Spend less.
Cyber incidents are inevitable, but extended downtime and spiraling recovery costs are not. Absolute Security transforms your recovery posture:
Automated, firmware-embedded recovery can cut incident response and device recovery expenses by more than 80%.

Restore devices to a trusted, operational state in minutes — not days — so business continuity is never in question.

Remediate and recover devices remotely and at scale, bypassing costly shipping and logistics headaches.
Most tools stop at the OS
Traditional endpoint security solutions are built on fragile ground, depending entirely on the operating system for installation, operation, and visibility. But when adversaries breach that layer or routine failures disrupt agents, your core protection, oversight, and control are instantly compromised.
Only Absolute Security's firmware-embedded approach ensures recovery isn’t dependent on the OS or agent health. True business resilience starts beneath the operating system so your endpoints, data, and ability to respond remain intact regardless of the attack.
Security that persists, not just protects
Absolute Security’s unique approach empowers organizations to restore operational command autonomously, without the delays and uncertainty of manual intervention. Our platform doesn’t just help you withstand the initial threat; it accelerates your recovery, reduces disruption, and safeguards productivity at scale.
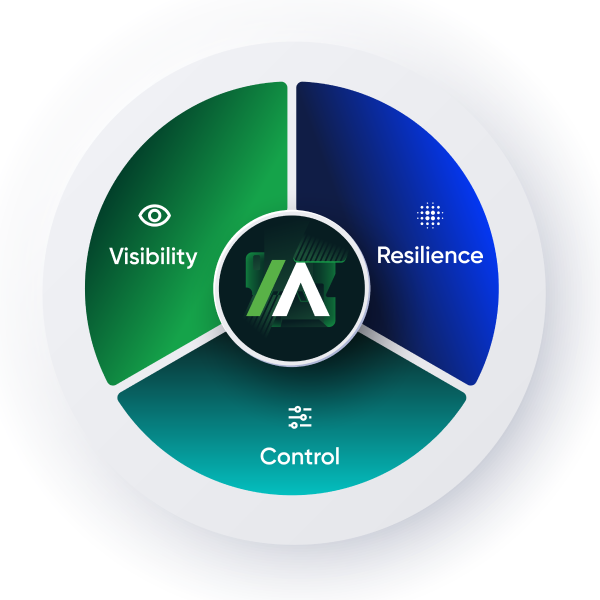
Visibility. Control. Resilience.
Powered by patented Persistence technology embedded in the firmware. Absolute Secure Endpoint gives your team an always-on connection to every endpoint to see risks, take action, and recover fast.
- Visibility: Know which devices are present, reachable, and healthy — whether they are on- or off-network.
- Control: Take immediate remote action to freeze devices, delete data, and reduce risk.
- Resilience: Automatically heal critical applications and restore what breaks or disappears.
Built in. Proven at scale.
Cyber resilience engineered into every device, proven across the world's most complex organizations.
Cannot be removed by re-imaging or hard drive replacement, keeping your security controls always intact.
Scalable for the world's most complex organizations, across every device and location.
Device recovery times cut from days to under 30 minutes — even after destructive attacks.
Security Service Edge (SSE) for the anywhere workforce
Resilient, reliable access to networks, cloud services, and private applications. Purpose-built to enforce Zero Trust policies for hybrid, mobile, and field workers.
- Reduce reliance on legacy VPNs and fragmented toolsets: Deliver always-on secure access to all apps, wherever users operate.
- Improve policy consistency for remote and hybrid users: Centralize, enforce, and adapt controls with unmatched agility.
- Accelerate compliance and reporting: Real-time dashboards and detailed analytics streamline governance and regulatory alignment.
- Safeguard productivity: Self-healing connectivity and proactive threat response keep users operational, even during attacks or outages.
Absolute Secure Access redefines how organizations protect the modern workforce, enabling businesses to move forward securely, without compromise.
Built for teams who can’t afford blind spots
Maintain control and visibility during disruption, ensuring your organization stays operational and compliant. Absolute Security delivers uninterrupted oversight, rapid recovery, and the assurance that business continuity is never at risk.
Cut manual recovery cycles and eliminate resource-draining reimaging. With Absolute Security, restore devices remotely, re-enable critical controls, and boost IT productivity. No user intervention or device retrieval required.
Strengthen a continuous, auditable security posture with real-time device visibility. Absolute enables swift remediation of compliance drift, helps enforce regulatory requirements, and simplifies audit readiness across your fleet.
Keep critical processes running and minimize business disruption, even if security controls fail or devices are unreachable. The Absolute platform ensures operational resilience, so productivity never stops.
Common questions, clear answers
An EDR is only effective when it’s operational. Absolute Security provides a resilience layer that complements existing EDR tools by ensuring endpoints remain reachable, recoverable, and secure even when OS-level tools fail or are disabled.
No. Absolute Security is more than just another agent. It’s a cyber resilience platform that consolidates and enhances endpoint security and management. It provides a unified, self-healing solution that ensures endpoints remain secure, visible, and operational — supporting your existing stack while reducing complexity and cost.
Secure Endpoint delivers device-level resilience, visibility, and control. Secure Access extends protection to cloud, web, and private apps, providing Zero Trust connectivity and regulatory compliance for the anywhere workforce.
See Absolute Security in action
Don’t let an incident expose your blind spots. Experience how self-healing endpoint security protects your system — before, during, and after an attack.
- Live product overview
- Tailored to your specific environment and fleet
- See Persistence and Secure Endpoint workflows live, including recovery from real attack scenarios