See how you stack up against other organizations in implementing the five pillars of the NIST Cybersecurity Framework: Identify, Protect, Detect, Respond, and Recover.
Download PDF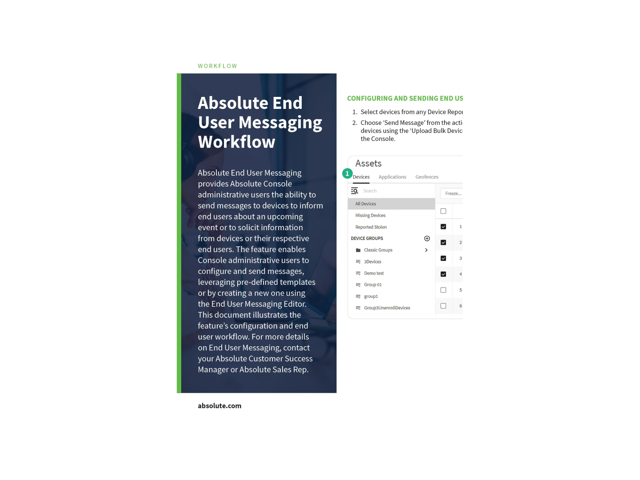
Learn how to send messages to devices to inform end users about an upcoming event, warn them of a policy violation or to solicit information from devices or their respective end users.
View ResourceTechnology in our schools enables modern learning paths, and brings a new level of innovation to the classroom. But it needs to be managed with care. Get insights into the K-12 cybersecurity crisis in this research report compiled from analyzing more than three million student devices over one year. View the infographic.
View Resource
Healthcare is data. Take these specific and practical steps for secure digital care and data protection across all your devices, no matter where they are.
View Resource