From IT Failure to Ransomware: Downtime Costs Millions

The problem
When an incident hits, the clock isn’t just ticking—your business is bleeding. Lateral movement accelerates, systems freeze, customers are impacted, and every minute of outage compounds financial & operational damage.
Most organizations rely on manual recovery steps. This leaves teams blind, controls offline, and operations at a standstill. Downtime doesn’t wait. Recovery shouldn’t either.
Rapid endpoint recovery matters
The numbers don't lie—and they’re getting worse. When incidents strike, the losses are immediate—and staggering. The following stats reveal just how high the stakes are.
Your disaster recovery strategy means nothing, unless you can control endpoint recovery securely. The alternative is a painstaking slog to manually restore each device individually, to ensure it doesn’t bring the whole network down again
Cybercrime and software failures cause disruptions that cost organizations more than a trillion dollars in losses annually.
How Absolute Security restores business continuity in minutes
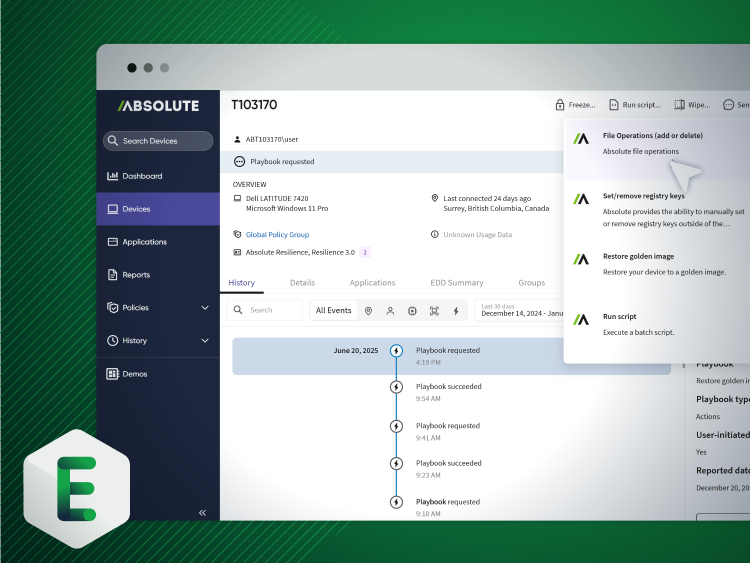
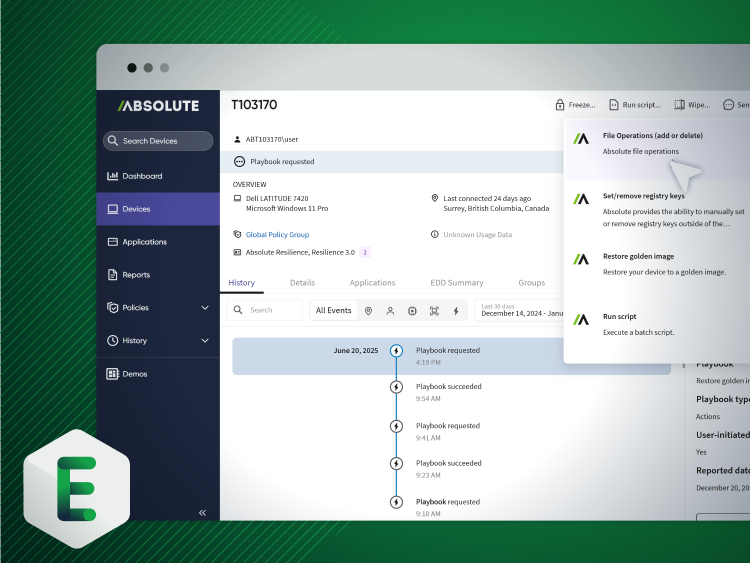
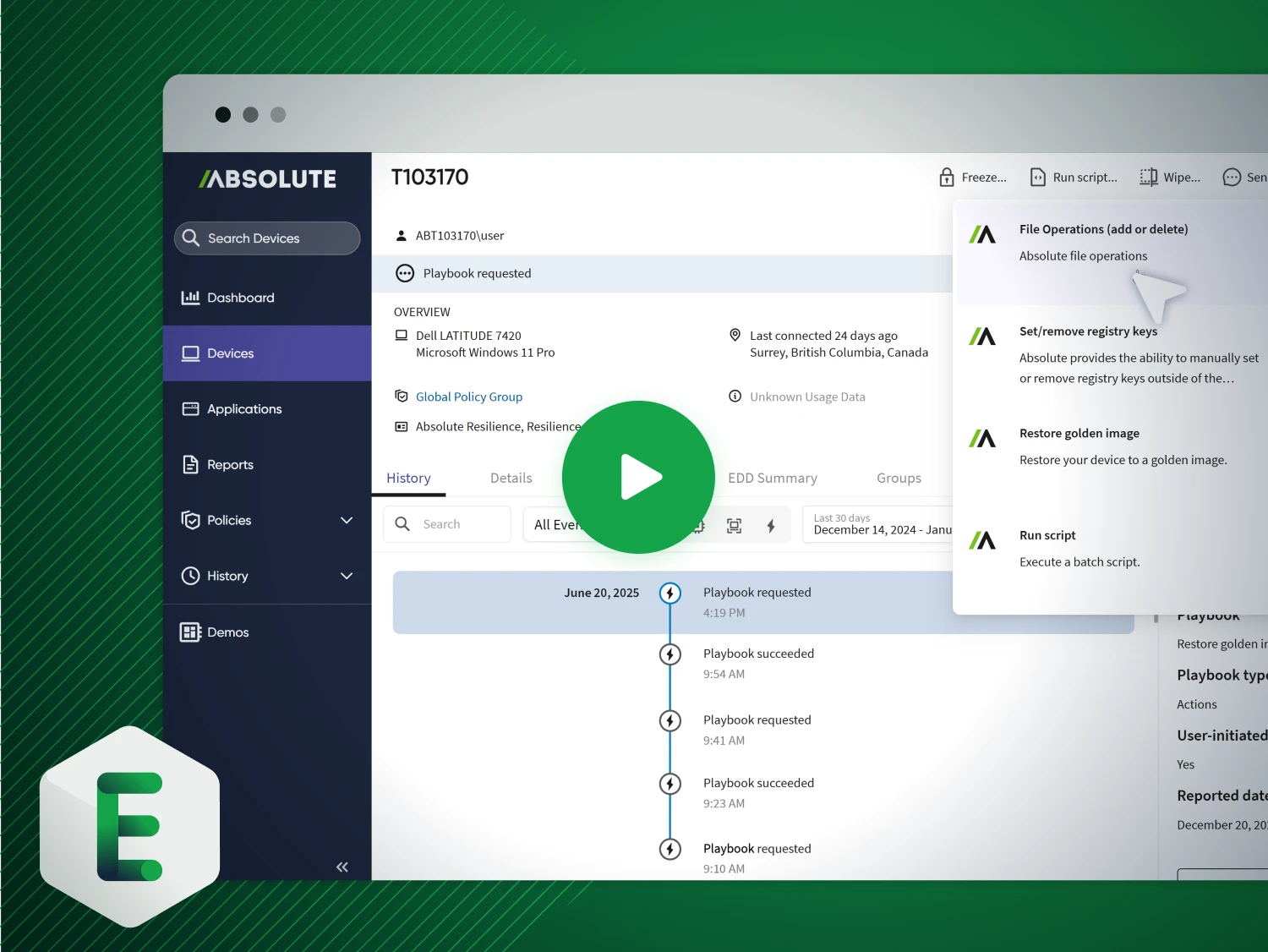
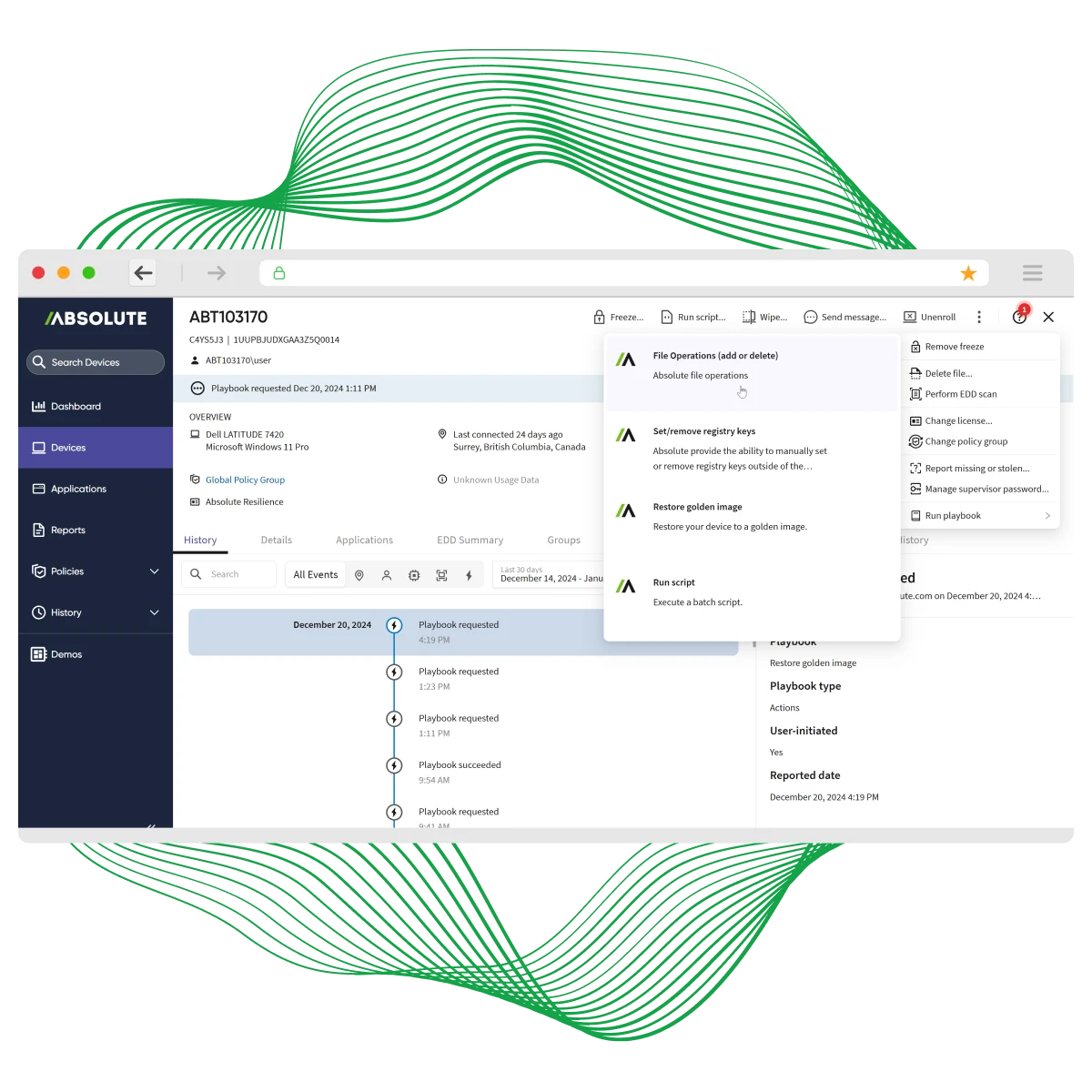
Absolute’s undeletable, self-healing connection—embedded in device firmware—guarantees access to every endpoint, even if it’s off-network, corrupted, or compromised. From anywhere, with a single click, you can isolate, freeze, or wipe compromised devices remotely. Trigger Absolute Rehydrate to restore a clean, trusted OS image and bring back operating systems, apps, and required controls with surgical precision—in minutes, not weeks. No desk visits. No shipping. No guessing.
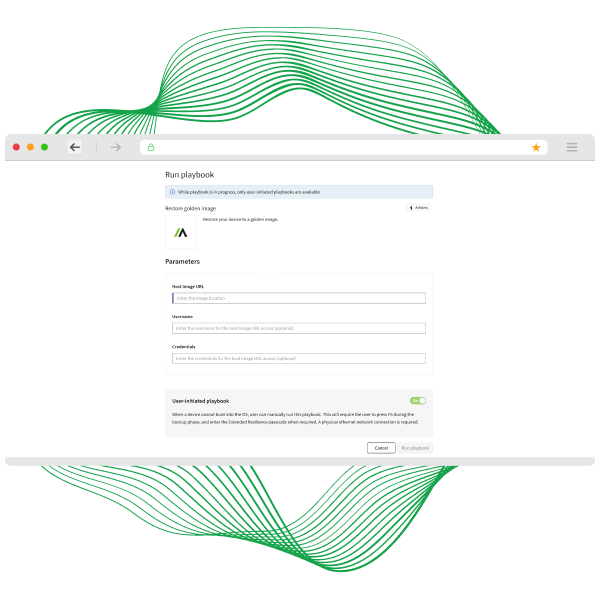
See Rehydrate in action
Stop letting incidents dictate downtime. Absolute Rehydrate restores compromised devices to a trusted, compliant state—fast enough to keep your business running without disruption.
- Rapid Recovery: Bring back OS, apps, and security controls in minutes—not hours or weeks—no desk visits, no shipping.
- Precision Restoration: Trigger a clean, verified OS image remotely for full compliance and operational continuity.


Umm Al-Qura University: cyber resilience and rapid recovery at scale
Managing thousands of endpoints across a sprawling campus, Umm Al-Qura University needed real-time visibility, control, and compliance—plus the ability to recover compromised devices fast. With Absolute Secure Endpoint, they strengthened security, streamlined IT operations, and gained the power to rehydrate endpoints remotely and at scale.
- Persistent Visibility & Control: Track device status, monitor software, and enforce security policies across thousands of endpoints.
- Rapid, Remote Recovery: Restore OS, apps, and security controls with Absolute Rehydrate—minimizing downtime and eliminating costly desk visits or shipping.
Key capabilities for remote recovery

Rapid endpoint restoration to a trusted state

Remote containment: wipe, lock, or network‑isolate compromised devices

Rollback failed patches and undo misconfigurations fast

Forensic data collection without interruption

Session termination & access revocation to enforce Zero Trust

Firmware‑embedded persistence for always‑on recovery—even during attacks
Fall in love with Rehydrate
Absolute doesn’t just recover endpoints—we rehydrate them, all before the OS even boots. Our firmware-embedded, tamper-proof agent makes recovery fast, secure, and cost-effective.
- Restore & Remediate: Instantly bring back a trusted image, apply fixes, and patch faulty software at scale.
- Cut Recovery Costs: See how Rehydrate reduces downtime and lowers recovery expenses by up to 80% in our whitepaper.
Experience resilient recovery firsthand
See the power of Absolute Rehydrate—built into the firmware of 600 million devices—for seamless setup and instant remote recovery at scale.
- Rehydrate with One Click: Restore your own devices, test custom playbooks, and access the full resilience platform.
- Prove Business Continuity: Evaluate impact on operations and define your POV goals with real-world recovery scenarios.
Featured resources for Accelerate Incident Response & Endpoint Recovery
Incident response & endpoint recovery FAQ
Ela acelera a recuperação porque muda as condições de base. Em vez de apenas reagir ao problema, a solução oferece uma conexão persistente e self-healing com cada endpoint. Isso permite executar ações críticas em minutos, e não em meses, como reverter um patch com falha, restaurar um dispositivo atingido por ransomware ou fazer remote wipe em um endpoint perdido para impedir uma violação de dados.
Ferramentas tradicionais costumam falhar quando agents são desativados ou perdem conexão, deixando a empresa cega justamente durante uma crise. Esta platform garante conectividade contínua e não removível, preservando acesso e controle o tempo todo. Trata-se de certeza e resilience quando isso realmente importa. Ela é compatível com uma ampla gama de PCs Windows, o que é especialmente importante para organizações empresariais com ambientes mistos de dispositivos. Além disso, o Rehydrate permite desde um reimage completo do Windows até ações mais cirúrgicas, como adicionar ou remover arquivos, modificar o registry ou executar scripts, tudo a partir de uma camada abaixo do operating system.
A implantação é rápida graças à tecnologia incorporada ao firmware presente na maioria dos dispositivos corporativos. Não é necessária infraestrutura complexa. Em geral, organizações entram em operação e começam a perceber valor em toda a frota em questão de dias, não de meses, alcançando resultados mais rápidos e mais resilience.
A Absolute ajuda empresas, órgãos governamentais e instituições de ensino que precisam de endpoint security contínua, aplicação de conformidade e mitigação de risco em tempo real.
Sim. Construída para escala global, a platform suporta frotas de milhares a centenas de milhares de dispositivos sem perda de desempenho. Visibilidade e controle em tempo real se estendem por toda a organização, independentemente do tamanho ou da geografia.
