From IT Failure to Ransomware: Downtime Costs Millions

The problem
When an incident hits, the clock isn’t just ticking—your business is bleeding. Lateral movement accelerates, systems freeze, customers are impacted, and every minute of outage compounds financial & operational damage.
Most organizations rely on manual recovery steps. This leaves teams blind, controls offline, and operations at a standstill. Downtime doesn’t wait. Recovery shouldn’t either.
Rapid endpoint recovery matters
The numbers don't lie—and they’re getting worse. When incidents strike, the losses are immediate—and staggering. The following stats reveal just how high the stakes are.
Your disaster recovery strategy means nothing, unless you can control endpoint recovery securely. The alternative is a painstaking slog to manually restore each device individually, to ensure it doesn’t bring the whole network down again
Cybercrime and software failures cause disruptions that cost organizations more than a trillion dollars in losses annually.
How Absolute Security restores business continuity in minutes
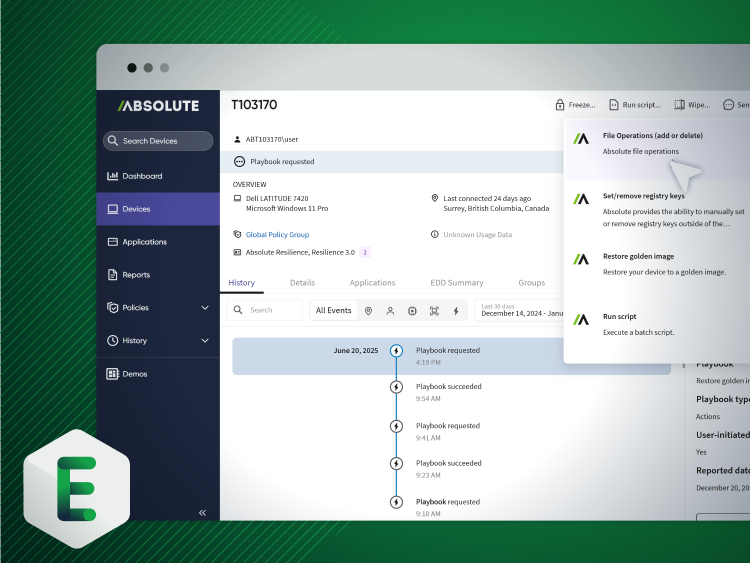
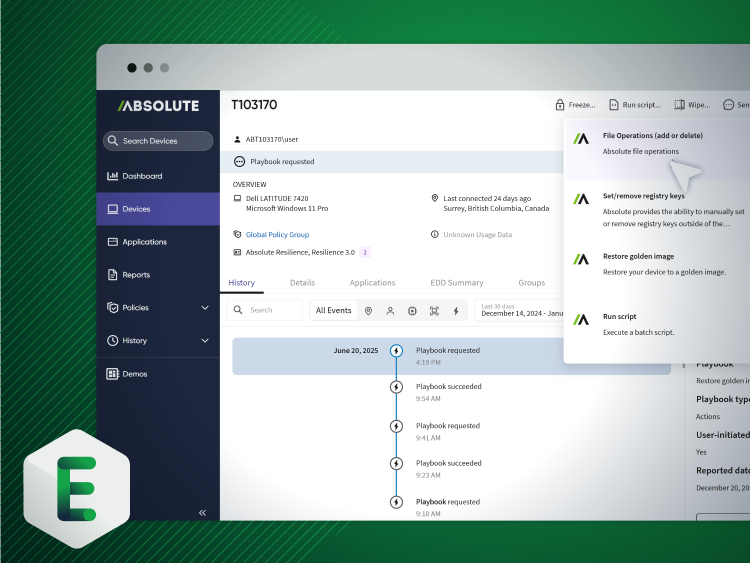
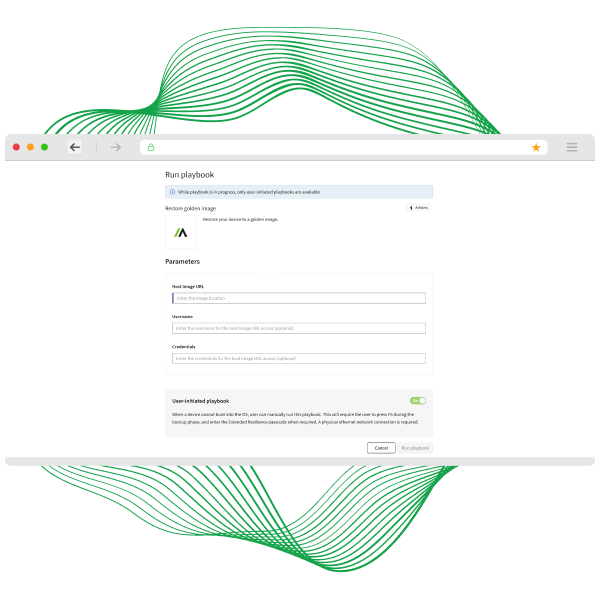
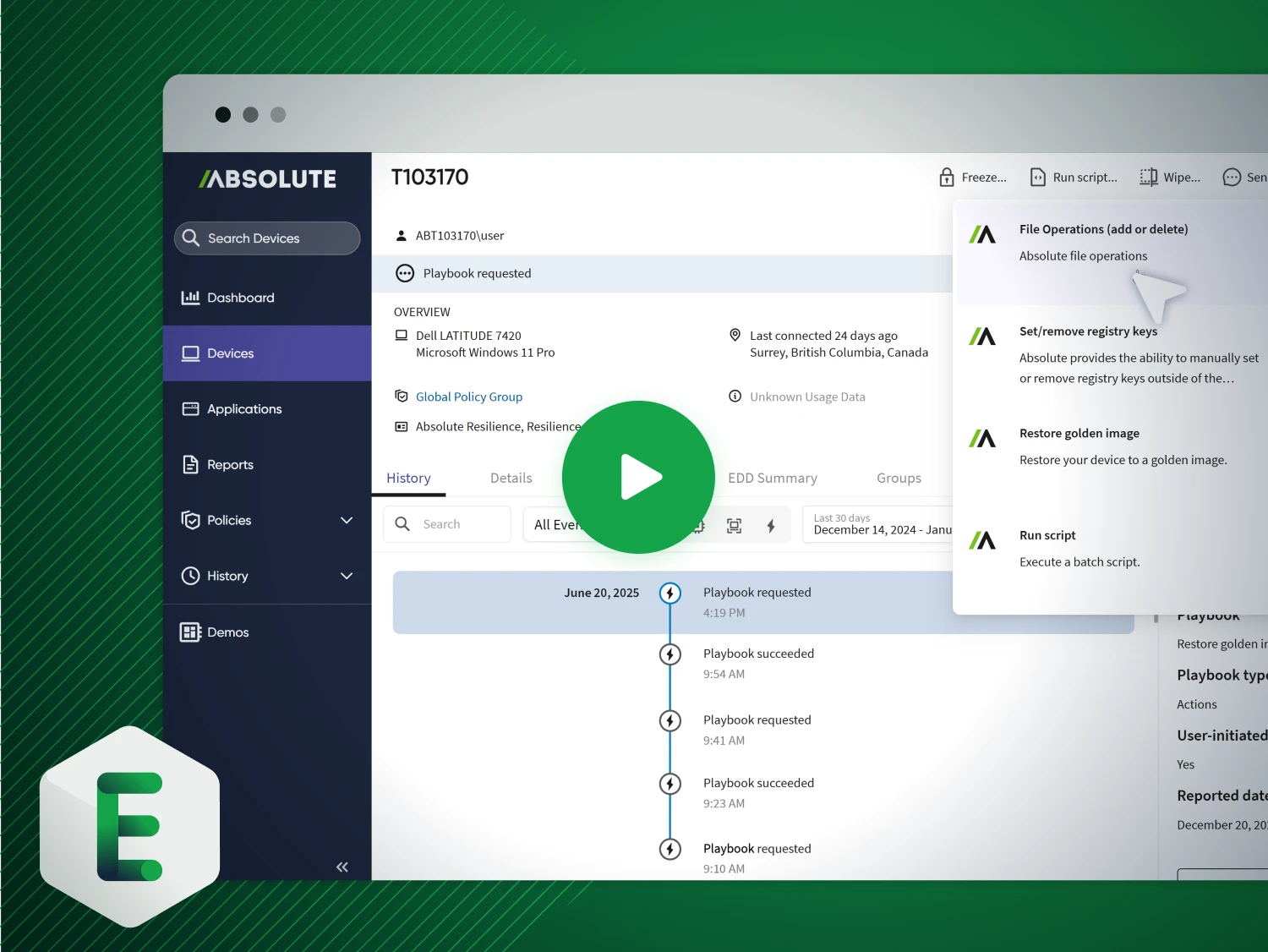
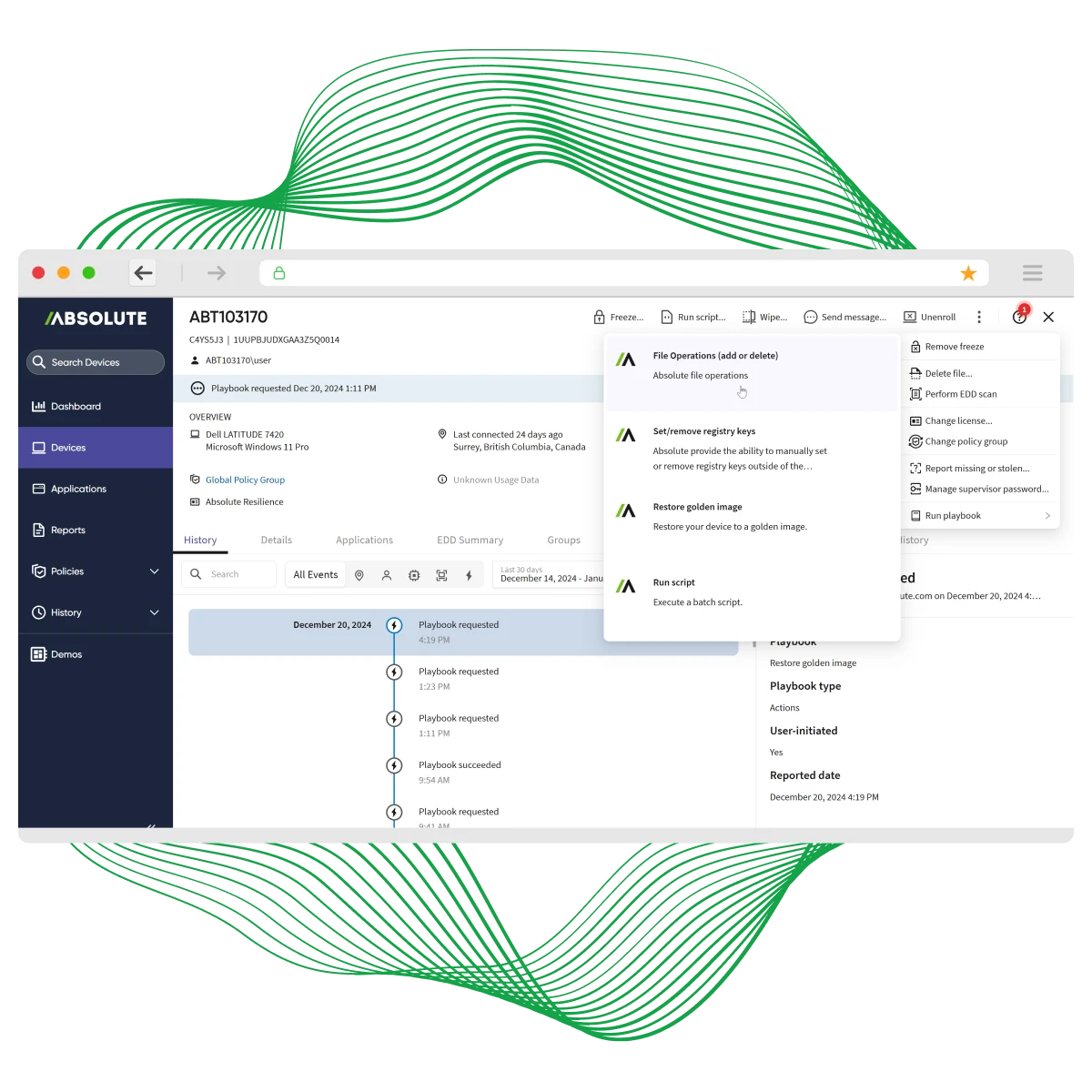
Absolute’s undeletable, self-healing connection—embedded in device firmware—guarantees access to every endpoint, even if it’s off-network, corrupted, or compromised. From anywhere, with a single click, you can isolate, freeze, or wipe compromised devices remotely. Trigger Absolute Rehydrate to restore a clean, trusted OS image and bring back operating systems, apps, and required controls with surgical precision—in minutes, not weeks. No desk visits. No shipping. No guessing.
See Rehydrate in action
Stop letting incidents dictate downtime. Absolute Rehydrate restores compromised devices to a trusted, compliant state—fast enough to keep your business running without disruption.
- Rapid Recovery: Bring back OS, apps, and security controls in minutes—not hours or weeks—no desk visits, no shipping.
- Precision Restoration: Trigger a clean, verified OS image remotely for full compliance and operational continuity.


Umm Al-Qura University: cyber resilience and rapid recovery at scale
Managing thousands of endpoints across a sprawling campus, Umm Al-Qura University needed real-time visibility, control, and compliance—plus the ability to recover compromised devices fast. With Absolute Secure Endpoint, they strengthened security, streamlined IT operations, and gained the power to rehydrate endpoints remotely and at scale.
- Persistent Visibility & Control: Track device status, monitor software, and enforce security policies across thousands of endpoints.
- Rapid, Remote Recovery: Restore OS, apps, and security controls with Absolute Rehydrate—minimizing downtime and eliminating costly desk visits or shipping.
Key capabilities for remote recovery

Rapid endpoint restoration to a trusted state

Remote containment: wipe, lock, or network‑isolate compromised devices

Rollback failed patches and undo misconfigurations fast

Forensic data collection without interruption

Session termination & access revocation to enforce Zero Trust

Firmware‑embedded persistence for always‑on recovery—even during attacks
Fall in love with Rehydrate
Absolute doesn’t just recover endpoints—we rehydrate them, all before the OS even boots. Our firmware-embedded, tamper-proof agent makes recovery fast, secure, and cost-effective.
- Restore & Remediate: Instantly bring back a trusted image, apply fixes, and patch faulty software at scale.
- Cut Recovery Costs: See how Rehydrate reduces downtime and lowers recovery expenses by up to 80% in our whitepaper.
Experience resilient recovery firsthand
See the power of Absolute Rehydrate—built into the firmware of 600 million devices—for seamless setup and instant remote recovery at scale.
- Rehydrate with One Click: Restore your own devices, test custom playbooks, and access the full resilience platform.
- Prove Business Continuity: Evaluate impact on operations and define your POV goals with real-world recovery scenarios.
Featured resources for Accelerate Incident Response & Endpoint Recovery
Incident response & endpoint recovery FAQ
復旧が加速するのは、前提条件そのものを変えるからです。単に事後対応するのではなく、このソリューションはすべてのendpointに対して永続的でself-healingな接続を提供します。これにより、重要なアクションを数か月ではなく数分で実行できます。たとえば、失敗したpatchのロールバック、ランサムウェア感染デバイスの復元、またはデータ侵害を防ぐための紛失endpointのリモートwipeなどです。
従来のツールは、agentが無効化されたり接続を失ったりすると機能しなくなり、危機の最中に企業が何も見えない状態に陥ることがあります。このplatformは、継続的かつ削除不可能な接続を確保し、常にアクセスと制御を保証します。重要なのは、まさに必要なときの確実性とresilienceです。さまざまなWindows PCに対応しているため、混在したplatform環境を持つエンタープライズ組織にとって特に有効です。さらに、Rehydrateでは、Windowsのフルreimageだけでなく、ファイルの追加・削除、registryの変更、scriptの実行といった、より細かなアクションも、すべてoperating system層の下から実行できます。
導入は非常に迅速です。多くのエンタープライズ向けデバイスにすでに存在する、ファームウェア組み込み型technologyを活用するためです。複雑なインフラは不要で、多くの組織は数か月ではなく数日で全フリートに展開し、価値を実感できます。より早い成果とresilienceの実現につながります。
Absoluteは、継続的なendpoint security、コンプライアンス適用、リアルタイムのリスク軽減を必要とする企業、政府機関、教育機関を支援しています。
はい。グローバル規模を前提に構築されており、数千台から数十万台規模のフリートでも、性能低下なく対応できます。リアルタイムの可視性と制御は、組織の規模や所在地に関係なく、全体にわたって拡張されます。
