From IT Failure to Ransomware: Downtime Costs Millions

The problem
When an incident hits, the clock isn’t just ticking—your business is bleeding. Lateral movement accelerates, systems freeze, customers are impacted, and every minute of outage compounds financial & operational damage.
Most organizations rely on manual recovery steps. This leaves teams blind, controls offline, and operations at a standstill. Downtime doesn’t wait. Recovery shouldn’t either.
Rapid endpoint recovery matters
The numbers don't lie—and they’re getting worse. When incidents strike, the losses are immediate—and staggering. The following stats reveal just how high the stakes are.
Your disaster recovery strategy means nothing, unless you can control endpoint recovery securely. The alternative is a painstaking slog to manually restore each device individually, to ensure it doesn’t bring the whole network down again
Cybercrime and software failures cause disruptions that cost organizations more than a trillion dollars in losses annually.
How Absolute Security restores business continuity in minutes
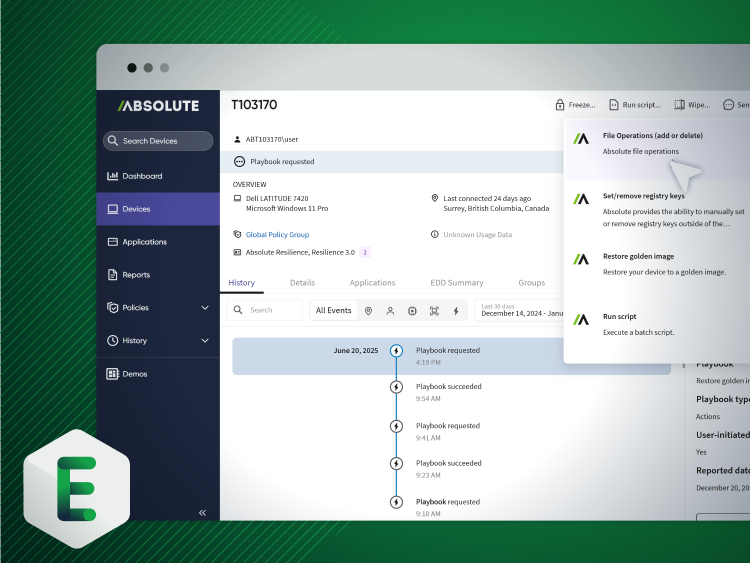
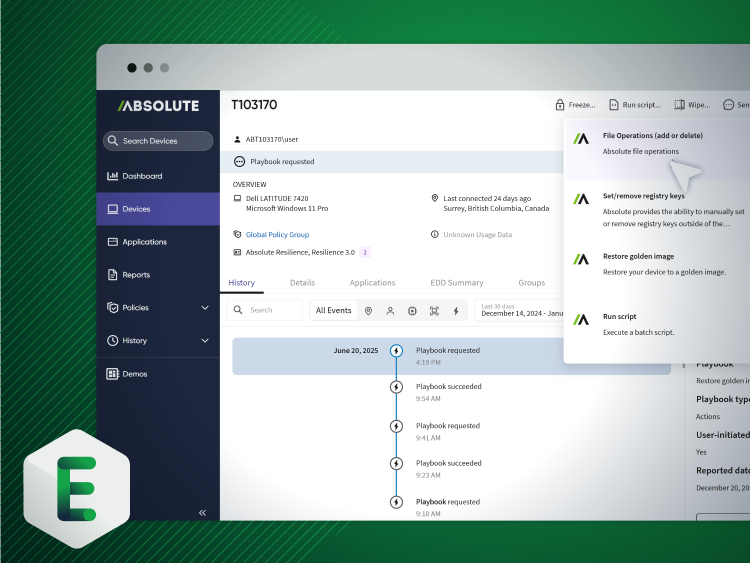
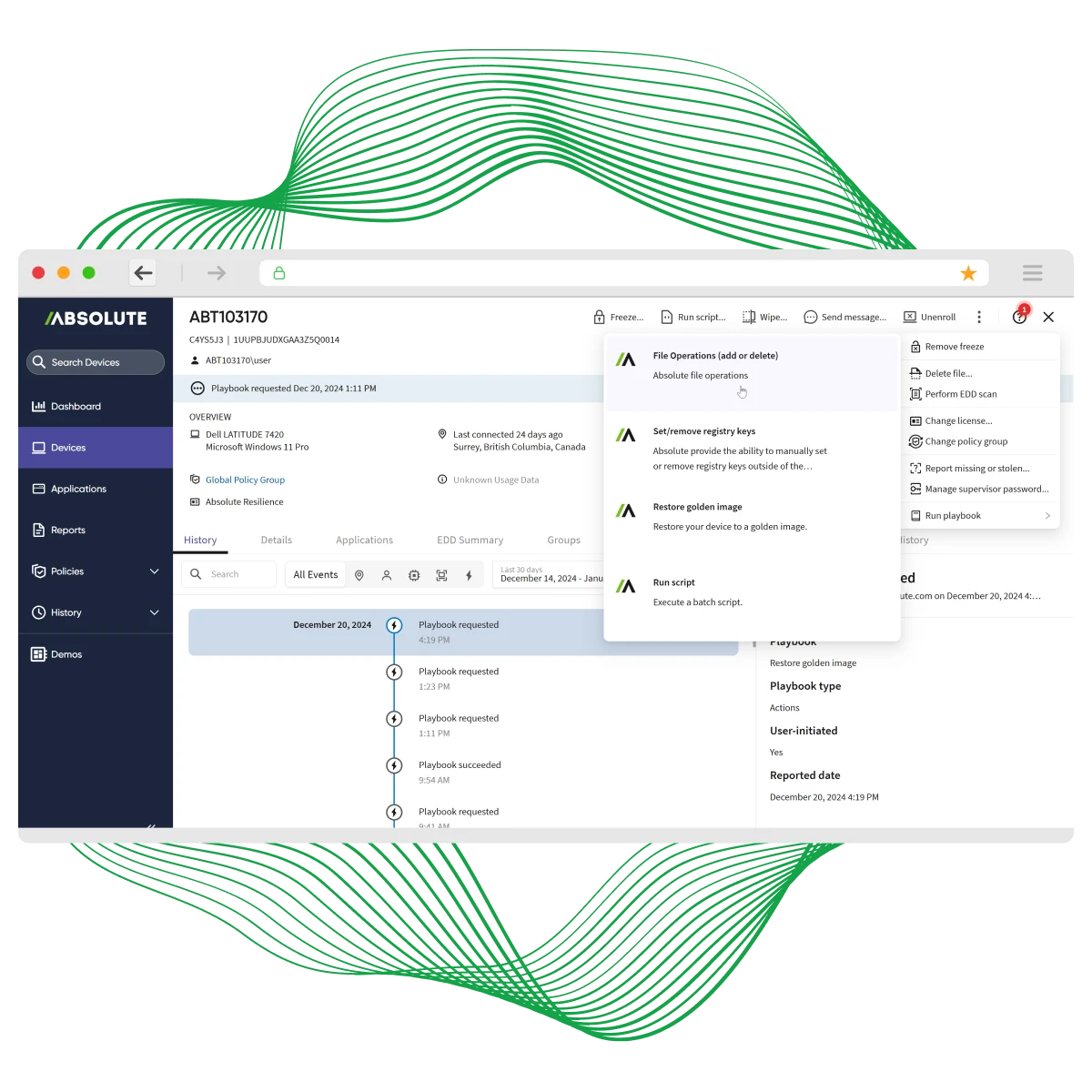
Absolute’s undeletable, self-healing connection—embedded in device firmware—guarantees access to every endpoint, even if it’s off-network, corrupted, or compromised. From anywhere, with a single click, you can isolate, freeze, or wipe compromised devices remotely. Trigger Absolute Rehydrate to restore a clean, trusted OS image and bring back operating systems, apps, and required controls with surgical precision—in minutes, not weeks. No desk visits. No shipping. No guessing.
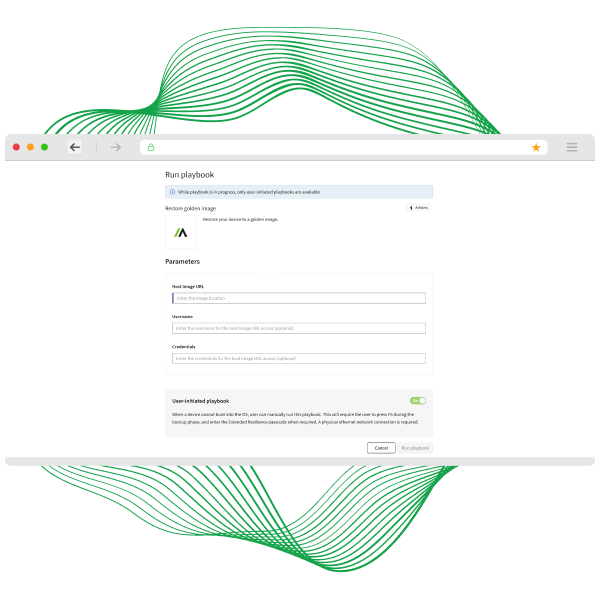
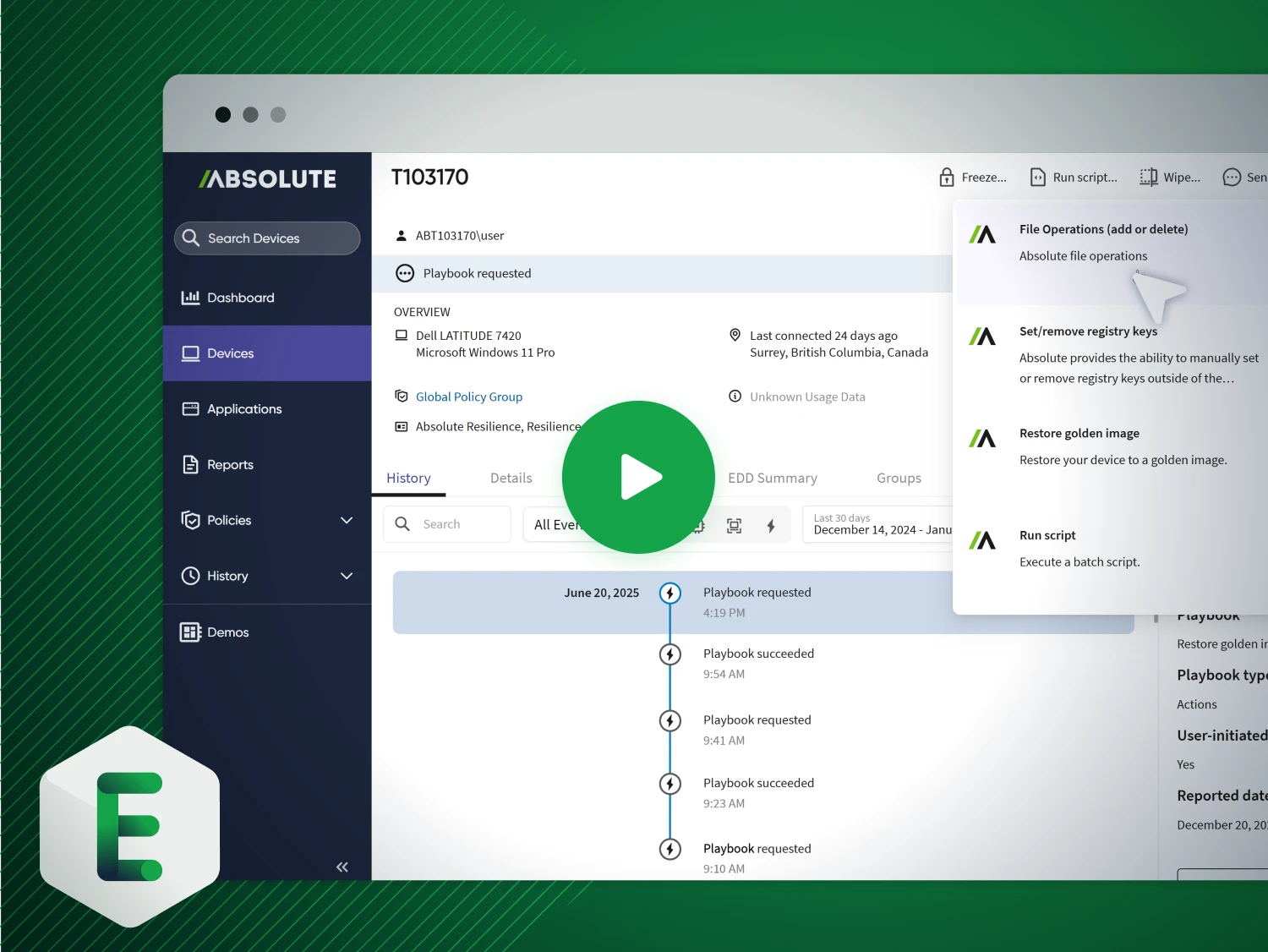
See Rehydrate in action
Stop letting incidents dictate downtime. Absolute Rehydrate restores compromised devices to a trusted, compliant state—fast enough to keep your business running without disruption.
- Rapid Recovery: Bring back OS, apps, and security controls in minutes—not hours or weeks—no desk visits, no shipping.
- Precision Restoration: Trigger a clean, verified OS image remotely for full compliance and operational continuity.


Umm Al-Qura University: cyber resilience and rapid recovery at scale
Managing thousands of endpoints across a sprawling campus, Umm Al-Qura University needed real-time visibility, control, and compliance—plus the ability to recover compromised devices fast. With Absolute Secure Endpoint, they strengthened security, streamlined IT operations, and gained the power to rehydrate endpoints remotely and at scale.
- Persistent Visibility & Control: Track device status, monitor software, and enforce security policies across thousands of endpoints.
- Rapid, Remote Recovery: Restore OS, apps, and security controls with Absolute Rehydrate—minimizing downtime and eliminating costly desk visits or shipping.
Key capabilities for remote recovery

Rapid endpoint restoration to a trusted state

Remote containment: wipe, lock, or network‑isolate compromised devices

Rollback failed patches and undo misconfigurations fast

Forensic data collection without interruption

Session termination & access revocation to enforce Zero Trust

Firmware‑embedded persistence for always‑on recovery—even during attacks
Fall in love with Rehydrate
Absolute doesn’t just recover endpoints—we rehydrate them, all before the OS even boots. Our firmware-embedded, tamper-proof agent makes recovery fast, secure, and cost-effective.
- Restore & Remediate: Instantly bring back a trusted image, apply fixes, and patch faulty software at scale.
- Cut Recovery Costs: See how Rehydrate reduces downtime and lowers recovery expenses by up to 80% in our whitepaper.
Experience resilient recovery firsthand
See the power of Absolute Rehydrate—built into the firmware of 600 million devices—for seamless setup and instant remote recovery at scale.
- Rehydrate with One Click: Restore your own devices, test custom playbooks, and access the full resilience platform.
- Prove Business Continuity: Evaluate impact on operations and define your POV goals with real-world recovery scenarios.
Featured resources for Accelerate Incident Response & Endpoint Recovery
Incident response & endpoint recovery FAQ
La recuperación se acelera al cambiar fundamentalmente la ecuación. En lugar de simplemente reaccionar, esta solución proporciona una conexión persistente y autorreparable con cada endpoint. Esto permite acciones críticas en minutos, no en meses: revertir parches fallidos, restaurar dispositivos infectados con ransomware o borrar de forma remota endpoints perdidos para prevenir filtraciones de datos.
Las herramientas tradicionales suelen fallar cuando los agentes se deshabilitan o pierden conexión, dejando a las empresas a ciegas en una crisis. Esta plataforma garantiza conectividad continua e imposible de eliminar, asegurando siempre el acceso y el control. Se trata de certeza y resiliencia cuando más importa. Es compatible con una amplia gama de PCs con Windows, lo cual es especialmente importante para organizaciones empresariales con entornos de dispositivos de plataformas mixtas. Además, Rehydrate ofrece la opción de realizar una reinstalación completa de Windows o acciones más quirúrgicas, como agregar o eliminar archivos, modificar el registro o ejecutar scripts, todo desde debajo de la capa del sistema operativo.
La implementación es rápida, gracias a la tecnología integrada en el firmware presente en la mayoría de los dispositivos empresariales. No se requiere infraestructura compleja. Las organizaciones normalmente entran en operación y obtienen valor en toda la flota en cuestión de días, no de meses, logrando resultados y resiliencia más rápido.
Absolute presta servicio a empresas, organismos gubernamentales e instituciones educativas que requieren seguridad persistente para endpoints, aplicación del cumplimiento y mitigación de riesgos en tiempo real.
Sí. Diseñada para una escala global, la plataforma admite flotas de miles a cientos de miles de dispositivos sin pérdida de rendimiento. La visibilidad y el control en tiempo real se extienden a toda la organización, sin importar su tamaño o ubicación geográfica.
