You Can’t Prevent Every Breach. You Can Stop Downtime.
Operational resilience that keeps endpoints working after cyber incidents.
Cyber incidents are inevitable.
What determines business impact is how long your organization is offline. Absolute Security eliminates downtime by remotely restoring compromised endpoints to a trusted, operational state — even when OS-level tools fail or are disabled.

"In the event of ransomware, malware, or system crashes (e.g., BSOD), Absolute Rehydrate enables our company to quickly return devices to a trusted state. This rapid recovery mechanism is crucial for maintaining business continuity and minimizing the impact of cyber incidents. It also supports proactive disaster recovery planning, ensuring that endpoint restoration is not dependent on functioning OS or network tools."
Downtime is the real cost of cyber incidents
Breaches make headlines, but downtime drains revenue. Most security stacks are built to detect and respond, not to restore operations. When endpoints fail, IT teams are forced into manual recovery workflows that extend disruption across the organization.
- Most organizations cannot restore endpoints at scale without significant operational downtime.
- Manual recovery processes often take days or weeks—multiplying disruption across distributed teams.
- Absolute Security customers reduce incident recovery costs by over 80% by eliminating downtime through automated recovery.

Most security tools leave you offline when it matters most
Security stacks are built to detect and respond, not to restore operations. When endpoints fail, IT teams are forced into manual recovery workflows that extend downtime across the organization. That gap between detection and recovery is where business disruption compounds.

Recovery that doesn’t depend on the OS
Absolute Security is embedded in the firmware of over 600 million devices, creating an always-on connection that survives attacks, failures, and misconfigurations. This unique position allows recovery even when operating systems, VPNs, or network tools are unavailable.
A secure, firmware-embedded connection that cannot be removed, disabled, or bypassed by bad actors.
Automated, remote restoration of compromised endpoints to a trusted state after incidents.
Recover thousands of devices simultaneously to eliminate organization-wide downtime.
Secure Endpoint: Resilience That Keeps Devices Working
Maintain visibility, control, and recoverability across endpoints on or off the corporate network so operations continue through disruption.
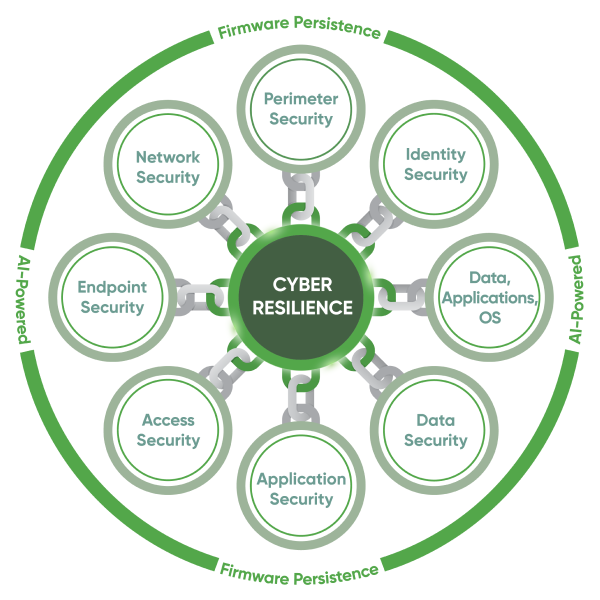
Secure Access: Security Service Edge (SSE) for the anywhere workforce
Resilient, reliable access to applications and data without introducing brittle dependencies that increase downtime risk.
See what stopping downtime looks like in your environment
- Live product overview
- Tailored to your specific environment and fleet
- Walk through downtime drivers and recovery assumptions specific to your organization








